Twitter Weekly Updates for EUdiscovery
March 11th, 2011 by Monique Altheim
- doesn't exactly encourage interfaith dialogue @Privacymatters re Belair & consumer advocates. needs bursary 2 help them b @ #IAPPsummit #
- RT @jlredd: Privacy on the Ground: MSFT back-of-the-envelop calc for privacy program costs per year: 13 million USD #iappsummit #
- At packed session on Interacting with the FTC, Robert Belair noted that not a single consumer/privacy advocate present #IAPPsummit #
- RT @PrivacySecurity: New EU web privacy law will require websites to get consent for cookies #
- #privacy #dataprotection RT @PrivacyLaw: EU: “New net rules set to make cookies crumble” http://bbc.in/hfpTNL #
- RT @WSJ: In this class, tweeting is required. Why businesses are sponsoring social-media courses at universities: http://on.wsj.com/gSxmwZ #
- Me too! RT @prefcentral: #privchat friends: who is attending #iappsummit this week? #
- Or else?RT @PrivacyDigest: RT @PrivacyMemes FTC urges ad industry: Take lead in online privacy issues http://bit.ly/fdMze7 #privacy #
- On my way to #iappsummit #
- All you ever wanted to know about EU data protection and ediscovery http://bit.ly/i5fkN6 #privacy #e-discovery #
- Spain's Parliament Modifies DPA Penalty Authority As DPA's Enforcement Efforts Scrutinized http://bit.ly/go4XxD #privacy #dataprotection #
- Hear ye, hear ye!! RT @DiscoverTERIS: NY Times Discovers e-Discovery, But Gets the Job Report Wrong http://bit.ly/ef77pp #ediscovery #
- Everything you always wanted to know about EU data protection and ediscovery http://bit.ly/i5fkN6 #privacy #e-discovery #
- Secrecy continues over EU's transfer of banking data to US http://bit.ly/g6N3KI #dataprotection #SWIFT #
- US businesses call for 'IQ alliance' with Europe http://bit.ly/gIZQUN #dataprotection #cloud #
- Supporters join case to uphold Vt. prescription privacy law http://bit.ly/ecx5wf #privacy #freespeech #
- Interesting point of view: Plan Now to Avoid Social Networking Data Silos http://bit.ly/haFx39 #CRM #socialmedia #privacy #
- Suit: Amazon fraudulently collects, shares users' personal info http://bit.ly/ed7vJY #privacy #dataprotection #
Privacy, European Union Data Protection and EDiscovery
March 6th, 2011 by Monique Altheim
Ediscovery in US Civil Litigation and EU Data ProtectionEDiscovery in the US
Electronic Discovery (or “Ediscovery”) is the process of identifying, preserving, collecting, preparing, reviewing, and producing electronically stored information (“ESI”) in the context of the legal process. Some examples of ESI are: emails, word documents, power point presentations, excel sheets, social media posts, voice mail and videos.
The legal basis for one party to request from the other party to produce ESI that are in that party’s possession, custody and control is Rule 34 of the Federal Rules of Civil Procedure. (2006):
“(a) In General. A party may serve on any other party a request within the scope of Rule 26(b):
(1) to produce and permit the requesting party or its representative to inspect, copy, test, or sample the following items in the responding party’s possession, custody, or control: (bold added)
(A) any designated documents or electronically stored information—including writings, drawings, graphs, charts, photographs, sound recordings, images, and other data or data compilations—stored in any medium from which information can be obtained either directly or, if necessary, after translation by the responding party into a reasonably usable form; or
(B) any designated tangible things; or
(2) to permit entry onto designated land or other property possessed or controlled by the responding party, so that the requesting party may inspect, measure, survey, photograph, test, or sample the property or any designated object or operation on it.”
In principle, any nonprivileged matter that is relevant to any party’s claim or defense, is subject to discovery, even if it is nor admissible as evidence, as long as it “may lead to the discovery of admissible evidence”, as per Rule 26(b):
“(b) Discovery Scope and Limits.
(1) Scope in General. Unless otherwise limited by court order, the scope of discovery is as follows: Parties may obtain discovery regarding any nonprivileged matter that is relevant to any party’s claim or defense—including the existence, description, nature, custody, condition, and location of any documents or other tangible things and the identity and location of persons who know of any discoverable matter. For good cause, the court may order discovery of any matter relevant to the subject matter involved in the action. Relevant information need not be admissible at the trial if the discovery appears reasonably calculated to lead to the discovery of admissible evidence. All discovery is subject to the limitations imposed by Rule 26(b)(2)(C) “.
The Courts interpret the Federal Rules of Civil Procedure as having extra-territorial reach.
As long as the ESI is in the “responding party’s possession, custody, or control”, and is relevant to the litigation, it does not matter wherein the world these ESI reside, it is discoverable under federal law. If, for example, a US employee can access ESI of an affiliate overseas on a shared network, the US company has “possession, custody and control”, and the overseas ESI is discoverable on that basis.
The US has the broadest civil discovery procedure in the world. None of the other Common Law countries, such as the United Kingdom, Australia and Canada, have such a wide scope of discovery and in most of the Civil Code countries, such as in most of the European and Latin American countries, the concept of discovery obligations is unknown.
In the last few years a quite voluminous case law has developed regarding the interpretation and application of the Federal Rule of Civil Procedure (FRCP). The law has developed differently in each of the District Courts and it is important to keep that in mind when preparing a case.
In cases governed by US state law, keep in mind that many states have enacted new civil procedure rules to cover discovery of ESI. Most states have adopted the FRCP ediscovery model. For example, Florida became the 29th state to adopt specific electronic data discovery rules for its state courts on July 5, 2012. It is based on the FRCP model.
When confronted with a lawsuit or subpoena in a large case, it is considered best practice to appoint a project manager, who organizes an eDiscovery team and who coordinates the co-operation between corporate counsel, IT, records management, HR, outside counsel and various service providers. This task can be done in-house, or outsourced to a law firm or an eDiscovery consultant.
The IT and records management departments are helpful in explaining the company’s IT architecture and the life cycle of the records, as well as in preparing a computer network and data map to locate all discoverable data. The endless list might contain servers, backup tapes, flash drives, laptops, iPods, smart phones, VOIP systems, EZpass data, IMS and text messages. It is important to consult HR concerning departed employees as well, since the EDiscovery process will typically cover a time period going back a few years.
If the information is not “reasonably” accessible, because of undue burden or cost, the parties are relieved from disclosure, (Rule 26 (b) (2) (B)), as they are when the burden or expense of the proposed discovery outweighs its likely benefit, the so-called “proportionality rule”. (Rule 26(b) (2) (C) (iii)).
Very old ESI, stored on obsolete media, might fall into the category of “unreasonably accessible”, and a case where the lawsuit is worth $100,000, but the EDiscovery costs would amount to $1 million, would fall into the category of “disproportionate”.
The data custodians then need to be interviewed to ascertain what relevant data they might have.
Once all the ESI at issue has roughly been identified, a “Litigation Hold” letter has to be sent to all relevant parties to make sure that the potential evidence doesn’t get destroyed or altered.
A “Litigation Hold” or a “Legal Hold” is a communication issued as a result of current or reasonably anticipated litigation, audit, government investigation, or other such matter that suspends the normal disposition or processing of records.
It is very important to carefully document all these steps, in case you have to prove due diligence in preserving ESI to the Court.
Then comes the ”meet and confer” meeting with opposing counsel and the Court, where parties discuss the scope of production of ESI in terms of subject matter and relevant time period. The following topics are some that also need to be addressed: the search methodologies to be used; the list of keywords to be used for keyword search; the requirement for preservation of metadata; the format for the production of ESI (TIFF or Native or both); clawback agreements (a clawback agreement is an agreement outlining procedures to be followed to protect against waiver of privilege or work product protection due to inadvertent production of documents or data); and issues of cost shifting (Rule 26 (f)).
Next, outside vendors or service providers are usually called in to perform the actual collection of ESI.
Some important questions to ask the vendors are whether they provide software that enables key word searching, conceptual searching, technology assisted searching, predictive coding, near duplicate identification, e-mail threading, and foreign language search capabilities. In smaller cases, in house IT staff may do the job of collecting all the ESI.
Once all the ESI is captured, the project manager arranges for teams of contract attorneys to review the ESI for relevance, and confidentiality and privilege flagging and redacting. This is the most time consuming and expensive part of eDiscovery. In a large lawsuit with about 30 million documents to be reviewed, this part of the eDiscovery process sometimes takes a few years to complete.
The reviewed data get analyzed by trial attorneys and integrated into trial preparation software.
Finally, the reviewed and analyzed ESI gets delivered to the opposing counsel in CD, DVD, hard drive or other formats, who then has his own team review the ESI.
In large cases, this whole procedure is executed in the form of rolling productions, with scheduled releases of data.
When eDiscovery needs to be executed outside of the US, for example in a foreign affiliate or subsidiary of a US company, the basic procedure remains the same, except that there are myriads of complications due to different legislations that apply when data gets collected in foreign jurisdictions.
Many countries outside of the US have legislation that protects data from either being collected and/or from being exported outside of the country.
These can be criminal laws, labor laws, bank secrecy laws, and data privacy laws.
The European Union data protection framework is one of the most prohibitive set of laws that parties to a civil litigation or government investigation in the US has to deal with, when trying to collect and export evidence.
EDiscovery in the EEA and Data Protection Issues
The EEA (European Economic Area) consists of the 27 member states of the EU, plus Iceland, Liechtenstein and Norway. It has one of the strictest data protection frameworks in the world.
In the EU, data protection is a human right and is protected by article 8 of the Charter of Fundamental Rights of The European Union.
The main legal instrument that regulates data protection in the EEA is the Data Protection Directive 95/46/EC.The Directive has been implemented by all 30 national member states into their national laws, and, while the Directive acts as a floor, some national laws have gone even further in their protection of personal data.
There are quite a lot of differences in implementation of the Directive: France, Germany, Spain, and Italy have stricter rules, while the UK has more lenient ones.
One of the most difficult problems of the EU data protection regime is the lack of harmonization of laws between the member states, and consequently also the difficult but important determination which national law is applicable in any given situation.
This is one of the points under consideration in the current process of overhaul of the entire European data protection regime.
On January 25, 2012, the European Commission proposed a new Data Protection Regulation. That Regulation should replace Directive 95/46/EC.
If the new legislation would indeed take on the form of a “Regulation”, it would be, under EU law, directly applicable to all member states, without need for separate implementation into national law, as would be the case for a “Directive” and that would considerably facilitate the global transfer of data outside the EEA.
Another proposed innovation would be the imposition of fines for data protection violation up to 2% of the gross annual turnover of the violating company.
It is expected to take quite a few years for the new rules to come into force though, so that for a while, the old rules will still apply and therefore will still be very relevant.
There is a serious conflict for US firms with affiliates in EEA countries, when they get involved in civil litigation within the US: On the one hand, federal and state rules mandate retention and production of all relevant data, even data located outside of the US, with the risk of severe penalties by the Courts in case of “spoliation”, and on the other hand, EU data protection laws (applicable to the EEA) mandate very strict data protection rules for “personal data” of their residents, that seriously restricts processing of personal data and transfer of those data to “non-adequate” countries outside of the EEA, with risks of steep fines in case of transgression.
Directive 95/46/EC regulates the processing of “personal data”.
“Personal data” is construed very broadly as “any information relating to an identified or identifiable natural person or “data subject”” (Article 2, (a) of Directive 95/46/EC).
For example, an email address is “personal data”.
“Sensitive Personal Data” are personal data that reveal “racial or ethnic origin, political opinions, religious or philosophical beliefs, trade-union membership, and the processing of data concerning health or sex life” and processing of such data is in principle prohibited, with a very limited list of exceptions ( Article 8 of Directive 95/46/EC).
The processing of personal data within the EEA is subject to extensive regulation, which, in a nutshell, strives to incorporate privacy principles, such as consent, access, proportionality, transparency, necessity and legitimacy. (Article 6 of Directive 95/46/EC).
The Article 29 Working Party, a EU data protection advisory body, recommends in its Working Document 1/2009 on pre-trial litigation in cross border ediscovery ( WP 158, 2009) guidelines to be followed in order to conduct cross border ediscovery within the requirements of the EU data protection framework.
It recommends that
- The filtering and reviewing of ESI for relevance should be done locally, within the EEA. Personal data should be anonymised or pseudonymised. The parties should obtain protective orders and filings under seal from the US courts to protect data from access by third parties.
- A notice should be sent to all employees or customers, whose emails or other data are collected. The data subject has a right to know that information is being collected about him/her.
- The data subject’s rights should be respected: for example, the data subject has the right to access the information that is being collected about him/her.
- Data Controllers should take reasonable measures to secure personal data from unauthorized access. This applies to vendors, law firms and courts in every stage of the ediscovery process.
- If the collection of ediscovery is outsourced to a third party, such as a vendor, there must be a written agreement with that third party, who must undertake strict confidentiality and provide appropriate security, must undertake to use the data only for specific purposes and within a specific retention period and only in accordance with the data controller’s instructions.
- There has to be a legal basis for processing of personal data. In other words, there has to be a legitimate reason to process personal data of other people: for example, curiosity is not a legitimate reason. For the purpose of ediscovery, there are only two legitimate basis for processing personal data under directive 95/46/EC: One is informed and freely given consent by the data subject (article 7 (a) ), the other is a legitimate interest of the data controller, balanced with the fundamental rights of the data subjects. (article 7 (f) ). The Article 29 Working Party recognizes ediscovery as a “legitimate interest”. For sensitive personal data, the legal basis is more stringent: consent is the only legitimate basis for purposes of ediscovery, and it has to be explicit and cannot be implied. For example, opt-out is implied consent, and opt-in is explicit consent.
- There has to be a legal basis for transfer of personal data outside of the EU. (articles 25 and 26). In the case of the US, this can be accomplished by several means: By receiving unambiguous consent from the data subjects (not very practical), by transferring the data to a Safe Harbor certified company in the US, by transferring the data under Standard Contractual Clauses agreements or by transferring them to companies that have “Binding Corporate Rules” in place. The question remains, however, how these personal data may be legally transferred onward to opposing counsel and to the Court. The Working Party recommends requesting a protective order from the Court, which guarantees the data a certain degree of privacy protection.
In order to show good faith, in case the national DPA should conduct an audit, it is to be recommended that the data controllers involved in ediscovery include all the above mentioned privacy guarantees in their general policies.
When choosing ediscovery vendor or consultants to do ediscovery in the EAA, one must look to how well they guarantee the rights of the data subjects under Directive 95/46/EC , such as notice to the concerned data subjects and access of the data subjects to their data and whether the processing of the data, such as preliminary document review, is done in the EU. When transferring data to the US for final processing, the US companies should either be Safe Harbor certified, or have model contract clauses or binding corporate rules, approved by the Data Protection Authorities, in place. This is a requirement for any EU personal data that will eventually be used in a civil proceeding in the US.
The increase of data protection risks associated with the rise of cloud computing has prompted the Article 29 Working Party to publish Opinion 05/2012 on Cloud Computing.
As a reminder tough, the Article 29 Working Party’s opinions are not legally binding, but they are very influential nevertheless.
Conclusion:
Companies which have to apply ediscovery rules and at the same time are under the jurisdiction of the EEA data protection laws, find themselves between a rock and a hard place.
Under Rule 37 FRCP and under the traditional rule of “spoliation”, which means the destruction or alteration of evidence, or even the failure to preserve property or documents for another’s use as evidence in pending or reasonably foreseeable litigation, the US federal courts have broad discretion regarding the type and degree of sanctions they can impose.
The sanctions run the gamut from significant monetary sanctions, to “adverse inferences”, meaning directing the jury to assume that missing ESI is adverse to the spoliator, to even default judgments.
As with other laws, the case law has developed differently in the different district courts.
In general though, the Courts do not look kindly, not only to those parties in litigation who are guilty of willful spoliation, but also those who merely show negligence in preserving and producing ESI, and the case law of Judges sanctioning negligent parties has grown over the past few years.
As mentioned before, these rules apply to all relevant ESI in the parties’ possession, custody or control, regardless of their geographical location or the applicable local laws.
It is therefore crucial for companies that are affiliates or subsidiaries of US companies, to have a litigation hold procedure in place, since the reasonable expectation of a lawsuit alone triggers the obligation of preservation of ESI under the FRCP, without delay.
What is even more crucial for companies today is the proper management of “information governance.”
Since storage of ESI has become so cheap, especially in the cloud, the lure for IT has been very strong to just store everything, forever. This can have disastrous consequences once a company gets involved in litigation or internal investigations, since, once the ball starts rolling, nothing potentially relevant may be deleted and as a consequence, a company may have to end up paying a small fortune for processing of terabytes of useless information.
It is a huge cost saving move for companies to invest in information governance. That involves, among others, the decision as to which data will be preserved for what period of time, and needs to be tailored to the needs of the company, depending on the type of industry and the regulatory and business requirements of the company. For most companies, there is no reason whatsoever to retain all low level employees’ emails, forever. There need to be a policy, stating for example that all of certain levels of employees’ emails need to be deleted within 6 months.
Proper information management will also facilitate the ability to locate data in an increasingly complex information ecosystem.
As far as EU data protection framework is concerned, the risk facing EU affiliates of companies from the US in the course of EDiscovery procedures not totally in line with the national data protection laws, consists of being investigated and maybe fined by the local Data Protection Authorities.
Of course, the risk depends very much on the country where the data are located.
If they are located in Germany, for example, the risks are much higher than if they are located in the UK.
Right now, most Data Protection Authorities are understaffed and under financed, and there have been complaints about lack of compliance and enforcement.
In France, for example, a January 2011 study has shown that 82% of French enterprises do not abide by the French Data Protection Act of 2004.
But with the overhaul of the EU data protection framework in full swing, and with the strengthening of the data subjects’ rights, as well as the improving of enforcement as some of the main objectives of the overhaul, I believe it would be wise for companies to prepare themselves and make sure they have the right infrastructure in place for proper compliance. The Federal Courts have already declared that social media are discoverable and that the mere fact of outsourcing IT to the cloud does not relieve companies from their EDiscovery obligations under the FRCP.
In cases where ediscovery requirements are irreconcilable with EU data protection requirements, companies will have to do a balancing test between the risks of non compliance with EU data protection laws and risks of non compliance with EDiscovery obligations in the US, on a case by case basis.
Or maybe it should be the Federal Courts and the Data Protection Authorities who should do the balancing when companies find themselves between the rock of ediscovery and the hard place of data protection.
This is exactly what Working Group 6 (WG 6) of The Sedona Conference® is suggesting in its 6 principles, “The Sedona Conference® International Principles on Discovery, Disclosure & Data Protection (December 2011).
WG 6 recommends that, as long as the parties in cross-border ediscovery show good faith and reasonableness, “US Courts, as well as Data Protection Authorities should consider the balancing of competing factors to achieve a practical compromise between the US litigants’ interests and the EU data subjects’ interests. “
The subject matter of cross border ediscovery is an extremely complicated one, and the move to mobile, social media and the cloud only complicates already very complex legal issues of applicable laws.
Twitter Weekly Updates for EUdiscovery
March 4th, 2011 by Monique Altheim
- CREDANT Technologies Research Shows: More Than 17,000 Usb Sticks taken to the Dry Cleaners In 2010 (UK) http:/… (cont) http://deck.ly/~kJPVY #
- Bills Push Medicare Data Access http://on.wsj.com/gkNK9v #privacy #
- IRS data: Privacy rights vs. finding the missing kids http://bit.ly/fsWKkV #
- Charlie Sheen more valuable? RT @nytimes: Proposed Cuts Strike Teachers as Attacks on Their Value to Society http://nyti.ms/hx1hZU #
- RT @HuffingtonPost: Bill to make 'touching junk' a felony http://huff.to/dPWkz4 #privacy #dignity #
- Home Office concedes Britain likely to become a surveillance state http://bit.ly/eqcs5C #privacy #
- #privacyright Peter Swire compares do not track to do not call. IMHO majior differences! #
- NOW! RT @JulesPolonetsky: Today Future of Privacy Forum web event! #Privacy Social Media & the Revolution?!… (cont) http://deck.ly/~GbOIb #
- EU Council Publishes Its Conclusions on the EU Commission's Communication on Personal Data http://bit.ly/eiyOvh #privacy #dataprotection #
- Microsoft Executive Urges Online Ad Industry to Police Itself http://on.wsj.com/hMyTNe #privacy #
- US Supreme Court rejects AT&T corporate privacy rights http://reut.rs/gtUNZo #
- RT @IntegreonEDD: Pulte Gets Pinched for Spoliation http://bit.ly/idImWF | @cspizzirri #ediscovery #
- #ediscovery #dataprotection RT @eMagSol: New York Appellate Court Refuses to Amend Confidentiality Order to Ad… (cont) http://deck.ly/~P8y0P #
- Thanks! RT @Tips4Tech: Shout-out #gratitude @Mike_Kunkle @EUdiscovery @WriteTheCompany @FortaliceLLC. #
- The Market for Online Privacy Heats Up – WSJ.com: http://on.wsj.com/dN9Bw5 #
- #oscars The King's Speech! Thank you UK Film Council,( too bad the British Gov has killed you with thrir cuts) #
- #oscars Colin Ferth! #
- Natalie Portman!! #oscars #
- #Oscars Tom Hooper: listen to your mom! #
- #oscars Tom Hooper: the triangle of man love #
- #oscars I <3 Anne Hatheway's wardrobe! #
- #oscars Inside Job!! So? Waddayagonnadoabouit? #
- #oscars God of Love! Yess! #
- #oscars Good speech, David Seidler #
- #oscars starting! #
- Mobile "conference" call: New Variants of 'Old' Symbian Mobile Spyware Emerge http://bit.ly/fC0CII #privacy #
- #Fcommerce RT @SmarterTravel: Do you "like" American's new Facebook frequent flyer offer? http://bit.ly/gsQwwK #
- Takes just as long to read, though! RT @PRC_Amber: #Facebook simplifies its #privacy policy (thank goodness) > http://bit.ly/gPMr89 #
- Thanks! RT @Tips4Tech: #FF Great! @privacyprof @EUdiscovery @FortaliceLLC @Mike_Kunkle @anthonymfreed @wiredla… (cont) http://deck.ly/~GuoEF #
- Thanks! RT @PogoWasRight: #FF #privacy @PRC_Amber @privacypug @LeighNakanishi @EUdiscovery @ARCH_Rights @Marie… (cont) http://deck.ly/~K0Qp8 #
- Are Companies at Risk for Astronomical Fines for Future EU Data Protection Violations? http://t.co/ZTKhWGt #
- Twitter Weekly Updates for EUdiscovery http://t.co/X1WFLi3 #privacy #ediscovery #socialmedia #
- EU's Hustinx: #DataProtection Law Sanctions Should Mirror Competition Law http://bit.ly/gnlZLW #privacy #
- Thnx! RT @JoannaMG22: #ff new contacts/chats @ransomthoughts @JaapVliet @Whit_CP_CEO @charlesteed @EUdiscover… (cont) http://deck.ly/~z2NG8 #
- Thanks! RT @LegalSPA: #FF @nuix_software @d4discovery @complexd @EUdiscovery @abatechshow @posselist @elitelink @ronfriedmann #
- Massachusetts General Hospital settles potential HIPAA violations http://bit.ly/ftlOjR #HIPAA #privacy #
- Irish #DataProtection Commissioner: top complaints 2 in 2010 abt failure 2 respond adequately 2 requests 4 acc… (cont) http://deck.ly/~pkhfH #
- Reps. See Red Over Reports of Google Data Collection From Kids http://bit.ly/hBRiI1 #privacy #
- Deloitte Issues Report on Data Privacy and Security in Health Care Industry http://bit.ly/fgPGBF #ehealth #HIPAA #HITECH #
Are Companies at Risk for Astronomical Fines for Future EU Data Protection Violations?
February 25th, 2011 by Monique Altheim
At a recent conference in Frankfurt, organized by the Internet Society,
Peter Hustinx, the European Data Protection Supervisor, suggested
sanctioning violations of the EU data protection laws with the same
astronomical fines as violations of competition laws are sanctioned.Henriette “Jetty” Tielemans, partner at the Brussels office of Covington & Burling LLP, reports as follows:
“The trade press regularly reports on multi-million euro fines for cartels or abuses of dominant positions by companies under the competition rules of the European Union. These figures are far away from the fines that currently can be levied for data protection violations. Observers of the competition law scene will agree that the main reason that companies operating in the EU pay attention to competition law is the astronomic fines that can – and are – levied.
Observers of the privacy scene also agree that one of the reasons that privacy is sometimes still not taken as seriously as it should by companies, is the relative lack of enforcement, and the low fines in case of enforcement. With shrinking legal budgets for compliance and training, companies often devote more resources to areas where fines are steep such as competition law.
Hustinx’s timing is not a coincidence. The European Union is reviewing the current 1995 Data Protection Directive and a draft proposal is expected this summer. Traditionally sanctions for violations of data protection laws have been left to the twenty-seven EU Member States (and they vary widely) but perhaps this will change. It remains to be seen how Hustinx’s suggestion will be received by the European Commission’s Data Protection Unit which is in charge of the revision of the 1995 Directive, subject to control by the European Parliament and the Council of Ministers. But the office of the European Data Protection Supervisor, charged with monitoring compliance by the European institutions of data protection rules within their own ranks and advising the European institutions on data protection issues, is influential and highly respected in the privacy community and this proposal will therefore not go by unnoticed. If accepted, it would revolutionize the data protection landscape in Europe.”
At present, compliance with the national data protection laws within the EU member states is less than satisfactory.
For example, as we reported recently on this website, 82% of French enterprises do not abide by the French Data Protection Act of 2004 (La Loi Informatique & Libertés).
Peter Hustinx’s suggestion should concern not only global companies with a physical presence in one or more EU member states, but also online businesses, websites and mobile applications that target the EU market, as we explained in this post on applicable law.
For our full overview of Peter Hustinx’s opinion in response to the Commission’s Communication of November 4, 2010 regarding the Review of the Data Protection Legal Framework , see here.
Twitter Weekly Updates for EUdiscovery
February 25th, 2011 by Monique Altheim
- RT @_deleteme_: I think you're enabling stalkers. #Spokeo #privchat RT @spokeo_com: We've updated our phone se… (cont) http://deck.ly/~e89WR #
- #Security shocker: Android apps send private data in clear http://bit.ly/gmdt8I #privacy #
- Google rescinds request for children's sensitive data http://usat.ly/fZtD42 #privacy #security #
- Preview Google's Apology for Collecting Kids SS#s http://bit.ly/idSmzD #privacy #
- EU outlines shortcomings in UK data law http://bit.ly/fdGpHl #privacy #dataprotection #
- Patients’ privacy threatened in NHS shake-up confidentiality under threat, say doctors (UK) http://bit.ly/eXG4eT #ehealth #
- Swiss Privacy watchdog takes Google to court http://bit.ly/h7YyHX #streetview #
- European Network and Information Security Agency ( ENISA) Publishes Report on Cookies http://bit.ly/hIkx7X #privacy #dataprotection #
- Passport Service breaches Data Protection Act (UK) http://bit.ly/hSwhqA #privacy #
- FTC Internet Privacy Proposal Slammed By Ad Industry http://bit.ly/faDWCy #dntrack #
- RT @datacenter: Report: Google Buys Land for Data Center in Taiwan. Local reports say project could include so… (cont) http://deck.ly/~rIoSV #
- "massive" ? no, but supercool RT @TheNextWeb: Upcoming Tech and Media Events with massive discounts http://j.mp/fD7WLX #
- nuBridges Unveils #TaaS a Hosted Data Tokenization Service http://bit.ly/i6L5iy #privacy #security #
- Some in Israel warn against Google Street View http://lat.ms/hgZvgF #privacy #security #
- reading: Privacy and genes, and worrying for patient privacy http://bit.ly/dWNWze #ehealth #
- OCR Plans to Tighten Up HITECH Privacy, Security, Breach Regs http://bit.ly/hEFRgI #HIPAA #
- RT @PrivacyLaw: “Privacy Please: Q&A With FTC Chairman Jon Leibowitz” http://bit.ly/eKqs4n #
- #ediscovery RT @RalphLosey: YouTube – Partner Asks for Help from Lit Support – http://bccth.is/cbg #
- RT @PrivacyCamp: Hey all @CFP11 (Computers, Freedom and #Privacy is starting up strong this year. Facebook Gr… (cont) http://deck.ly/~UWqg0 #
- RT @osocialmedia: Twitter Restores 3 UberMedia Apps After Privacy Concerns http://ow.ly/1brapt #
- Just created a resume from LinkedIn : meet the resume; cool http://bit.ly/gqBJDL #
- RT @Dystopia2009: RT @LossofPrivacy Loss of Privacy Daily is out! http://bit.ly/dkA8nL ▸ Top stories today @eu… (cont) http://deck.ly/~TotGX #
- RT @Forbes: 5 reasons why your online presence could soon replace your resume http://bit.ly/frHfzh #
- #ediscovery RT @PrivacyMemes: Facebook Photos Help Nail U.K. Tax Cheat http://bit.ly/dMTzCA #privacy #
- Gartner: by Year-End 2013, 1/2 of All Companies Will Have Been Asked to Produce Material from #SocialMedia Web… (cont) http://deck.ly/~MCBNU #
- Web users need more cookie contro (Enisa report) http://bit.ly/hyiZaN #privacy #dataprotection #
- The RFID Privacy and DataProtection Impact Assessment Framework in the EU: The Article 29 Working Party and th… (cont) http://deck.ly/~zDQBJ #
- Hong Kong hospital staff member lost a USB flash drive containing patients' data http://bit.ly/fnVWqx #privacy #ehealth #
- BYOD to work but be prepared for remote wipes and legal holds, says Unisys http://bit.ly/iblmEn #privacy #
- i disabled web history a while ago, but forgot- too much, too complicated-need to simplify in busy livesRT @Ju… (cont) http://deck.ly/~p3VOH #
- Thanks! RT @JulesPolonetsky: @EUdiscovery http://bit.ly/cB2cmh turn off personal search #
- I had no idea…now I know. still have no choice…RT @JulesPolonetsky: my issue is that people should know wh… (cont) http://deck.ly/~PXuPA #
- The RFID Privacy and Data Protection Impact Assessment Framework in the EU: The Article 29 Working Party an… (cont) http://deck.ly/~eQkzM #
- RT @TRUSTe: Lincoln National fined $600K for lax data security http://ow.ly/3ZeQR #
- Thankks for #FF #privacy ! @Tips4Tech #
- U.S. patients trust docs, but not e-health records, survey shows http://bit.ly/eqxPgE #privacy #HIPAA #ehealth #
- Jarvis: Publicness Needs Its Advocates, Just Like Privacy http://bit.ly/hjrOuA -no, not in a world that's public by default #
- Study Raises Concerns About Security Measures for Clinical Trial Data (Canada)http://bit.ly/hfqFT7 #privacy #
- BC Commissioner: In a networked world, privacy is still a priority http://bit.ly/dFlSIg #dataprotection #
- HHS announces contract for data privacy pilot http://bit.ly/fNJLuP #
- MMIC Offers Data Privacy Insurance http://bit.ly/f0dEsd – create a need, then provide a solution? #
- Twitter Weekly Updates for @EUdiscovery http://t.co/A66qMcw #
- thx RT @bbw1984: #ff @bourney2 @therealkyeleigh @dollymixture @lodsatrouble @canoewolf @lohiole @wc2a_2ae @tomi01uk @molecule18 @eudiscovery #
The RFID Privacy and Data Protection Impact Assessment Framework in the EU: The Article 29 Working Party and the FTC are in No Rush
February 19th, 2011 by Monique Altheim
On
February 11, the Article 29 Working Party adopted an opinion on the
revised Industry Proposal for a Privacy and Data Protection Impact
Assessment (PIA) Framework for RFID applications. (ARTICLE
29 DATA PROTECTION WORKING PARTY 00327/11/EN WP 180 Opinion 9/2011 on
the revised Industry Proposal for a Privacy and Data Protection Impact
Assessment Framework for RFID Applications)The aricle 29 WP endorses the proposal developed by industry associations, experts, academics, and individual companies from across Europe.
One of the main privacy concerns related to RFID technology arises from uses of RFID technology which entail individual tracking and obtaining access to personal data. While an RFID operator may not have such a goal in mind when deploying an RFID application, it is important to consider the risk that a third party may use tags for such unintended purposes. The revised framework now clearly requires RFID operators to evaluate the risks that may arise when tags may be used outside the operational perimeter of an RFID application and/or are carried by persons.
The European Commission published a recommendation on the implementation of privacy and data protection principles in applications supported by radio-frequency identification on May 12th, 2009.( the “RFID Recommendation”).
One of the recommendations reads:
“Article 7: RFID use in Retail
Article 7.3: (a) Where a RFID application processes personal data or the privacy impact assessment…shows significant likelihood of personal data being generated from the use of the application, the retailer has to follow the criteria to make the processing legitimate as laid down in directive 95/46 and to deactivate the RFID tag at the point of sale unless the consumer chooses to keep the tag operational. (b) Where a RFID application does not involve processing of personal data and where the privacy impact assessment has shown negligible risk of personal data being generated through the application, the retailer must provide an easily accessible facility to deactivate or remove the tag.”
In the U.S. Federal Trade Commission Comments on the the European Commission’s recommendation of May 2009, the FTC stated, in response to recommendation Article 7.3: (a)
” …Similarly, with respect to RFID, we caution against mandating a specific technological approach, such as mandatory deactivation of tags, before fully understanding the range of benefits the technology might provide to consumers, as well as the range of protective measures that might be available to consumers in the future.”
(The U.S. Federal Trade Commission’s Bureau of Consumer Protection is in charge of protecting consumer rights in the US.)
This is the recent Article 29 WP’s opinion on the subject matter of RFID use in retail:
“This concern (about individual tracking and access to personal data) has received particular attention in the retail sector, where it is feared that tagged items bought by individuals could be misused by retailers or third parties for tracking or profiling purposes. The European Commission addressed this concern in the Recommendation by establishing the principle that tags must be deactivated at the point of sale unless the customers give their informed consent to keep tags operational. The same Recommendation allows an exception to this deactivation principle if the PIA concludes that keeping tags operational after the point of sale does not represent a likely threat to privacy or the protection of personal data. The Working Party observes that a risk management approach, as suggested by the Framework, is an essential tool for the RFID Operator to assess the risks of taking the responsibility to keep tags activated after the point of sale.”
As shown with this example, a key point is that the Revised Framework is based on a risk management approach, which is an essential component of any Privacy and Data Protection Impact Assessment Framework.
The Article 29 WP however would like see implementaion of the Commission’s recommendation no earlier than three years from now.( 2014):
“The European Commission is expected to provide a report on the implementation of the Recommendation, its effectiveness and its impact on operators and consumers, with regards in particular to measures concerning the retail sector. This report is set to be produced 3 years after the Recommendation was published, that is by May 2012. However, considering that the Framework may take 6 months to fully take effect, supplementary time would be beneficial for all stakeholders before such an evaluation is conducted. Therefore, the Working Party would like to suggest to the European Commission to either postpone or supplement the proposed report at a later date set in 3 years from the publication of this opinion.”
In the above mentioned comments on the the European Commission’s recommendation of May 2009, the FTC remarked:
“The FTC staff supports the EC’s risk- based approach to addressing potential consumer privacy and data security issues related to the use of RFID technology. The FTC staff also agrees with the EC that there is a need to raise consumer awareness about RFID technology, in order to enhance consumer trust and to give consumers the tools to protect themselves from the risk of misuse of their information. Given the current stage of deployment of consumer-facing RFID applications, however, the FTC believes that mandating or encouraging specific technological tools for protecting consumer privacy is premature.” (bold added)
Premature?
Implementation no earlier than 2014?
Last summer, Wal-Mart created quite a controversy when it started to use RFID tags to track underwear and jeans and the George Miller III Head Start Program in Contra Costa County, California, created a buzz when they started to make pre-schoolers wear jerseys, with RFID chips inside that track them through the day.
But RFID (Radio frequency identification) technology is far from new. It has been used for many years to keep track of cattle, prisoners, goods, and pets.
RFID technology is already widely adopted, world wide and in many industries, and is also found in enhanced driver’s licenses, credit and debit cards, passports and government IDs, TWIC Cards, Employer ID/Proximity Cards, US EZpasses, London Oyster cards, just to name a few applications.
The risk of tracking, profiling, fraud, identity theft is here and it is real. RFID readers are used by convenience stores, pharmacies, restaurants, fast food markets, bars, and many other places of business to read the RFID chips.
However, these same readers can be freely purchased and attached to a laptop with very little technical knowledge required. There are even cell phones with built in card readers that can steal your information. By simply walking past you, anyone equipped with such a device can acquire your credit card number and expiration date. There is even a term for it: electronic pick pocketing.
Here’s a not so recent video by Boingboingtv’: “How to hack RFID-enabled Credit Cards for $8 (BBtv)”
Human RFID Implants are already used for access to car, home, office.
Human RFID implants with personal health and financial information are being used and promoted:
Premature? Seriously?
Twitter Weekly Updates for EUdiscovery
February 18th, 2011 by Monique Altheim
- good morning? RT @GlobalPigeon: blog post – Government of the rich, by the rich, for the rich http://econ.st/h8GQGy #
- RT @InfoGovernance: Socha & Gelbman Go High Tech – http://tinyurl.com/45up23j (Monica Bay) #ediscovery #
- Karl Theodor Maria Nikolaus Johann Jacob Philipp Franz Joseph Sylvester von und zu Guttenberg-what a name http://bit.ly/dTxu9z #
- Highlights of #PrivChat 2.15.11 by @privacycamp http://t.co/DkjBAtx #
- Thanks! @PrivacyCamp #
- Healthcare Social Media Sites Neglect Privacy Protections http://bit.ly/i6hjbR #
- Can Facebook-Addicted Congressmen Force Themselves to Crack Down on the Social Network? http://t.co/wTnWBGT via @forbes #
- Shoddy Anti Derivatives Reform “Study” From Firm That Falsely Claimed Top Academics as Advisor http://bit.ly/how6dn #
- Digital Signage: Privacy in a 'One-Way Mirror Society' http://bit.ly/h1KdVz #
- Additional defendants in Apple class action suit http://bit.ly/gU2ztX #privacy #apps #
- Full-Body Scan Privacy Law Gets One Step Closer To Reality http://bit.ly/hjA4wp #
- White House undecided about data retention law http://cnet.co/gPi4ie #privacy #
- Privacy in the Cloud: A Legal Framework for Moving Personal Data to the Cloud http://bit.ly/f6f0Hq #privacy #dataprotection #
- Watchdog finds Vodafone breached Privacy Act (Australia) http://bit.ly/fuSCGX #security #dataprotection #
- RT @bbw1984: European Parliament adopts common sense approach to web blocking –> http://is.gd/WYhHgc #
- RT @InfoGovernance: NIST Issues Draft Guidelines on Security and Privacy in the Cloud – http://tinyurl.com/4wj84nu (Bob Ambrogi) #
- RT @keshoo_: Keshoo Daily is out! http://bit.ly/ihFjb6 ▸ Top stories today via @eudiscovery @sectorprivate #
- #privacy RT @PrivacyCDN: http://is.gd/Yl1Mq1 Facebook Data of 1.2 Million Users from 2005 Released: Limited Exposure, but Very Problematic #
- #fcommerce RT @LanaMcGilvray: Interesting data on why people follow brands on Facebook http://ht.ly/3UVMA #facebook #branding #
- #socialcommerce RT @mashable: PayPal Founder: Facebook Could Become the Most Valuable Company in the World – http://on.mash.to/gDAtLy #
- #sicialcommerce RT @mashable: PayPal Founder: Facebook Could Become the Most Valuable Company in the World – http://on.mash.to/gDAtLy #
- RT @oceanpark: posted my annotated bibliography on sns privacy & surveillance for cybersurveillance workshop http://bit.ly/dFW5OW #
- Great to actually "see" you! free "invisible"speech is not free speech@clarinette02 #privchat #
- RT @PRC_Amber Our approach is that the more people know about #privacy the more they'll see a need for baseline legislation [1/2] #PrivChat #
- #privchat A5: excellent video for teen edu http://bit.ly/gdrk0G #
- #privchat draw attention to FB's latest default settings re visibility http://bit.ly/gZW9Ie #
- #privchat free speach de facto curtailed bcse u don't bite the hand that feeds you #
- A2; good area to compare with EU-differences mind bogging #privchat #
- good idea !RT @JamieXML: @CenDemTech Ok, will take that as a nudge for serious analysis of the Rush bill. (You too Monique
 )..#privchat. #
)..#privchat. # - don't think so RT @JamieXML: @CenDemTech Wow. Ambitious. Anything out there as a prototype? Similar to the EU directive? #privchat #
- #privchat Monique Altheim, US & EU attorney, blog at http://ediscoverymap.com #
- Thanks RT @CenDemTech: @EUdiscovery I …I'll try to get them out sooner next week -Mark S., CDT #
- How abt more advance notice of topics RT @CenDemTech: #PrivChat staring in about 20 min. Here are today's topics http://bit.ly/9Cz09j #
- Data privacy bill gets initial OK (Philippines) http://bit.ly/gA8J6G #dataprotection #
- #Dataprotection law may be added next year (Singapore) http://bit.ly/hp5m2U #privacy #
- Man decides to open source his genetic data using GitHub http://bit.ly/hxW8El #privacy #
- What topics? RT @PrivacyCamp: Noon today ! #PrivChat on #Privacy Noon ET – (Please Share) #
- Does Facebook's lack of transparency violate the right to free speech & to impart inform. ? http://bit.ly/gZW9Ie #privchat (my blog post) #
- Reading "Technology, Human Rights and Public Policy: Some Views From Europe" http://bit.ly/iivFPV #privacy #
- With CPOs like these…Prescriptions and Privacy http://bit.ly/e5LzNd #
- What about virtual husbands?RT @TheNextWeb: Indian Website Offers Virtual Wives http://tnw.to/17SNN by @francistan on @Shareables #
- RT @TheNextWeb: Chinese microblogging service Sina Weibo outguns Twitter with voicemail and direct video uploads http://tnw.to/17SLm #
- RT @RalphLosey: Jason and I talk about e-discovery education, the Sedona Conference, and some of our upcoming projects. http://bccth.is/bZy #
- RT @traveldeals: $118/night & up – Le Meridien Cambridge in Cambridge, MA – 36% Off – http://bit.ly/hjnVjV #
- yes please RT @TheNextWeb: Will the iPhone 5 adopt a 4-inch screen to keep up with Android? http://bit.ly/dNph32 #
- RT @ehasbrouck: Bilingual ad 4 Berlin protest 16/2 against data retention, Internet blocking, govt use of #PNR data: http://bit.ly/hDFBpW #
- RT @OpenCongress: We're getting a new Senate Judiciary subcommittee. "Subcommittee on Privacy, Technology & the Law." http://bit.ly/fVMvhf #
- How Will The 2 New Proposed #Privacy Bills Protect You? http://snipr.com/21r7ev #
- Google Seeks Social Networking Face Recognition Patent http://bit.ly/fBb88w #privacy #
- RT @DataPrivacyDay: … use "Exposed," CEOP's new video on sexting, to discuss protecting privacy with teens. http://bit.ly/hePkDE #privacy #
- Health Data Stolen From New York City Hospitals -1.7 million patients' data involved http://on.wsj.com/f1g4w7 #HIPAA #databreach #privacy #
- Thnx! RT @Tips4Tech: #FF #privacy: @PrivChat @PrivacyProf @CyberSafety808 @CyberSafeFamily @EUdiscovery … @jdp23 @JulesPolonetsky. #
- Thnx! RT @InfoLawGroup: #FF @EUDiscovery @_OBASHI @xDD0Sx @PogoWasRight @PrivacyCamp @WhatTheyKnow @sameerpandania @ProfJohnathan #
- RT @PrivacyMemes: German Government Budgets 10 Million EUR to Set Up #DataProtection Foundation http://bit.ly/fImqsr #privacy #
- RT @IntegreonEDD: Metadata Maintained by Agency as Part of Electronic Record is Producible under #FOIA http://bit.ly/hedQNo #ediscovery #
- RT @DavidNavetta: BEST PRACTICE Act is back!; we did a 2 part FAQ on the bill: Pt.1 http://bit.ly/9tvBoK; Pt.2 http://bit.ly/bvF6Vn #privacy #
- Thanks @mkais7 @tombolt @robertbrogan @CyndyTrivella @Gulpfish @joannawolfe re : Blogging #hfchat #
- Q5; #hfchat does blogging get you noticed by recruiters? #
- "Do Not Track Me" online bill introduced in Congress today by Rep. Jackie Speier http://bit.ly/eG3mQK #privacyb #DNTrack #
- RT @PrivacyCamp: Storing customer's ZIP code violates California law, high court rules – Sacramento Bee http://ow.ly/3UMHe #privacy #
- Thanks for RTs ! @PRC_Amber @econwriter5 @WC2A_2AE @curtiskj @privacyala @PrivacyQueen @privacyesq @hrucic @nicfab @robincaron (2/2) #
- Thanks for RTs ! @keshoo_ @myiddotcom @louwiseman @LossofPrivacy @legalift @anbusch @TomEtty @PrivacyCamp (1/2) #
- Thnx! RT @PrivacyWonk: FF #Privacy @CenDemTech @PrivacyCamp @clarinette02 @DataPrivacyDay @alexanderhanff @EUdiscovery @PogoWasRight #
- Thanks! RT @LegalSPA: #FF @sfldata @EDiscoveryMap @TrialSolutions @EUdiscovery @discoverapplied #
- My weekly Twitter updates http://bit.ly/eTmze2 #privacy #ediscovery #socialmedia #
- Facebook decides who gets to view your posts and whose post you get to view http://bit.ly/gZW9Ie #Socialmedia #cenorship #privacy #
- Does FB get to decide who gets to view your posts and whose post you get to view? http://bit.ly/gZW9Ie #censorship #socialmedia #privacy #
Twitter Weekly Updates for EUdiscovery
February 11th, 2011 by Monique Altheim
- RT @nytimes: NYT NEWS ALERT: Mubarak Clings to Office; Crowds in Cairo Are Furious #
- finally the E-word! RT @SophieToupie: is it ethical to be mining people's data or not? #privacy2011 #
- Court of Appeal: Warrantless Search of Car’s SDM is violation of 4th amendment http://bit.ly/e08KbJ #privacy #
- Sensing and Diagnostic Modules (SDM) in cars and #privacy http://bit.ly/ge0IKQ #ediscovery #
- Korea: Corporations Remiss in #Privacy Protection http://bit.ly/gOvmVo #
- Databreach in recruitment site in Ireland, leaking around 400,000 email addresses in the process. http://bit.ly/gPhQ4g #privacy #
- Google Adds Cellphone-Based #Security For Everyone http://bit.ly/gaf8l5 #privacy #
- very cool! but waht abt #privacy RT @IsCool: Just set up my > Doodle: MeetMe | Shaun Dakin http://ow.ly/3U4rK – online calendar #
- How To: Delete Personal Data from Photos on Windows and Mac http://bit.ly/fLicZh #privacy #
- Another sneaky FB move to control and censure your feed http://on.fb.me/hyfsyP #
- FTC Commissioner: If Companies Don’t Protect Privacy, We’ll Go To Congress http://bit.ly/hT9g3J #
- RT @privacyguru: Interesting….Facebook limits developers to preferred advertisers list http://bit.ly/hS4rxk #
- FTC Posts Guidance for Providers and Insurers on Medical Identity Theft http://bit.ly/gBLCn2 #privacy #
- What abt priest/penitent privilege?#privacy RT @sharonnelsonesq: Catholic bishop approves Confession iPhone app: http://tinyurl.com/6z5qmcf #
- U.S. Sens. Schumer and Nelson propose bill to make the misuse of airport body scan images a federal crime http://bit.ly/fheqea #[privacy #
- New Study: Most Google, Facebook users fret over privacy http://usat.ly/h4CvEg #
- #privacy RT @bikespoke: Insurance Investigators Guide to Claim Investigations and Social Media http://bit.ly/fGtIgo #privchat #socialmedia #
- Deutsche Post DHL the first German company to have their BCRs for data protection recognized by EU officials http://bit.ly/he5ow6 #privacy #
- sorry for joining so late #privchat Q5 Today is Safe Internet Day in EU: check it out http://bit.ly/gP8koz #
- Banks not taking credit card data security seriously: Survey http://bit.ly/f2GKfw #India #dataprotection #outsourcing #
- Judge Hands Spokeo A Victory In #Privacy Lawsuit http://bit.ly/g9Gidz #dataprotection #
- It's Super Bowl Sunday, do you know who's watching you watch the game? http://bit.ly/dR8ssK #tracking #profiling #datamining #privacy #
- New Data on Attitudes Toward Targeting http://bit.ly/g3vHQp #DNtrack #privacy #
- This is SO cool! RT @jasnwilsn: RT @capitaltoomey: A social network graph of #LTNY tweets. http://flic.kr/p/9ftjdB …#ediscovery #sna #
- RT @ComplexD: Judge Compels Discovery of ICE Databases – http://tinyurl.com/4r3yepu (Adam Klasfeld) #eDiscovery #
- RT @PRC_Amber Excellent post by @PogoWasRight: "Ranking People Search Websites: How rank are they?" http://bit.ly/eSMAVs #privacy #
- Rep. Speier to introduce 'do not track' bill next week http://bit.ly/gkYwN7 #privacy #privacytheater #makebelieveprivacy #
- RT @privacyfocused: Privacy Lives: Op-ed at Los Angeles Times: Your Rx or your privacy http://bit.ly/eML7BD #
- #Privacy and #DataProtection in the EU: The grass is not always greener on the other side of the pond http://bit.ly/hWzemL -my latest post #
- EDRi supports #EU #dataprotection REGULATION http://bit.ly/i0dtwp #privacy #
- Application Provides Privacy for Geotagged Digital Pictures – deGeo http://bit.ly/hac7rm #geolocation #geotagging #geofencing #
- Art 'dating site' steals 1m Facebook profiles http://bit.ly/gE3r9V #privacy #valentinesdayspecial #
- Why "Permission Marketing" Is the Future of Online Advertising http://on.mash.to/fpCTPx #cultofthesocial #socialgraphmarketing #
- NHS (UK) 'misleads patients' over sharing medical records with drug firms http://bit.ly/eW4W7H #privacy #dataprotection #ehealth #
- RT @jfehrman: Laptops, Portable Media Represent Leading Cause of HIPAA Data Breaches http://bit.ly/gpXBjh #encryption #privacy #
- RT @PrivacyWonk: Check out @CenDemTech's newest privacy tip! Health 2.0, HIPAA, and you: http://bit.ly/fvaFf1 #
Facebook and the First Amendment: Facebook decides who gets to view your posts and whose post you get to view
February 11th, 2011 by Monique Altheim
In a bold new move, Facebook has
taken on the role of content censor on its own platform, and has done so
in its notoriously sneaky style.
It is by chance that I learned about the change in my Facebook settings, thanks to the fact that I am lucky enough to be connected to some of the thought leaders in the Privacy field, such as Rebecca Herold, also known as @PrivacyProf. She posted a note on her wall today, which I will reproduce below to give the authors the credit they deserve.
It is by chance that I learned about the change in my Facebook settings, thanks to the fact that I am lucky enough to be connected to some of the thought leaders in the Privacy field, such as Rebecca Herold, also known as @PrivacyProf. She posted a note on her wall today, which I will reproduce below to give the authors the credit they deserve.
NEW FACEBOOK SETTINGS RESTRICTING YOUR VIEWING PLEASURE!
Info shared by Abby Smith – thanks Abby!)
Have you noticed that you are only seeing updates in your newsfeed from the same people lately? Have you also noticed that when you post things like status messages, photos and links, the same circle of people are commenting and everyone else seems to be ignoring you?
Don’t worry, everyone still loves you and nobody has intentionally blocked you. The problem is that a large chunk of your friend/fan list can’t see anything you post because the “New Facebook” has a newsfeed setting that, by default, is automatically set to ONLY SHOW POSTS FROM PEOPLE WHO YOU’VE RECENTLY INTERACTED WITH OR INTERACTED WITH THE MOST (which would be limited to the couple of weeks just before people started switching to the new profile).
So in other words, for both business and personal pages, unless your friends/fans commented on one of your posts within those few weeks or vice versa – you are now invisible to them and they are invisible to you!
HERE’S THE FIX:
Scroll down to the bottom of the Newsfeed on your HOME page and click on “Edit Options”. In the popup, click on the dropdown menu next to ‘Show posts from:’and select “All Of Your Friends and Pages” and then click Save.
Note: This is the fix for personal pages but I am unsure of whether or not the business pages are set up the same way.
Simply posting an update about it won’t do any good because lots of your friends/fans already can’t see your posts by default. You’ll either have to send out a message to everyone on your list (which I’m not even sure business pages can do and is a rather tedious method) or post an event explaining the situation like this one and invite your entire fan base and/or friend list. You can also tweet about it hoping that most of your fellow facebookers are also on twitter.
PLEASE FEEL FREE TO SHARE THIS NOTE WITH AS MANY PEOPLE AS YOU CAN SO WE CAN TRY AND GET EVERYONE INFORMED AS SOON AS POSSIBLE. Anyone who isn’t seeing your posts right now will never see them until they have changed their settings as explained above.
Here is a screenshot I took of my Facebook Home page to illustrate Tracie’s excellent explanation:
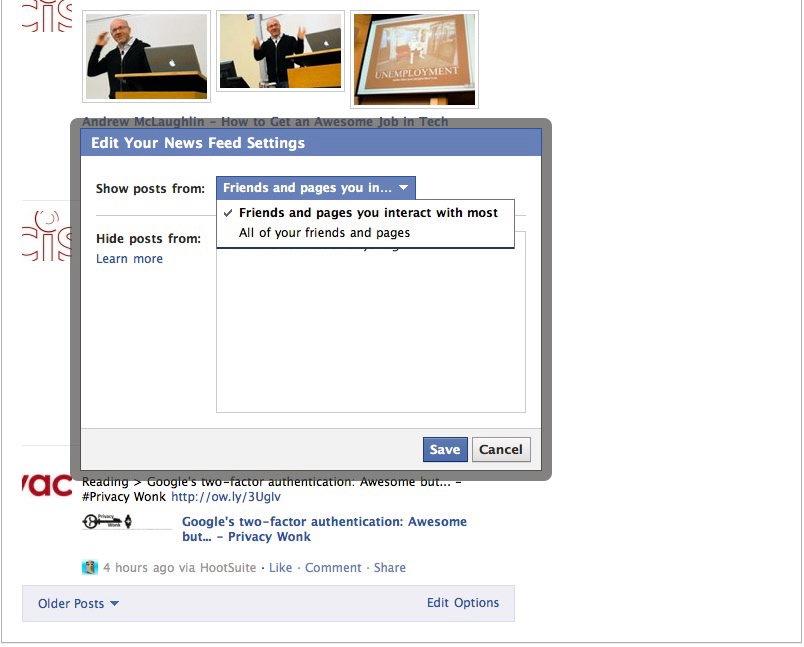
As you can see, my default setting was set by Facebook to show posts from”Friends and pages you interact with most”. Of course, I changed it immediately to show posts from “All your friends and pages”. None of my Facebook friends were aware of this default setting, and most of them are professionals, very well informed in social media matters.
After changing the default setting, I learned that one of my friends’ daughters was Bat-mitzvahd, through a post that was hidden from me before I changed that setting, because this friend very rarely posts on Facebook. Another Facebook friend learned, only after changing her setting, that her cousin had a new baby.
This latest move by Facebook seriously worries me:
In my opinion, it smacks of censorship as practiced by the worst kind of despots. By introducing this kind of default setting and , on top of that, by not notifying users of this change, Facebook is basically deciding for its 600 million users what they can and cannot see on its platform.
What is the motivation behind this latest change? More profit for Facebook, no doubt, even though I fail to grasp the exact logic behind it.
I have understood by now, that as much as I want to believe, (or maybe Facebook wants me to believe) that I am the one using Facebook for my benefit, it is in reality Facebook that is using me for its benefit.
Facebook’s tactics of taking away our privacy and our choices, little by little, reminds me of the tactics used by the most dangerous tyrants in human history.
This excellent German video about the dangers of a sureveillance state, illustrates those tactics, as applied by governments.
It explains the traditional metaphor of the frog: when frogs are put in a tub of hot water, they instinctively jump out, because it hurts too much (except on Glenn Beck’s show, where they die instantly). Frogs that are put in a tub of cold water stay, even after the temperature slowly increases until they cook alive. So it is with people. When surveillance is increased slowly, people don’t revolt. They just adapt, and refrain from showing and exptressing differing attitudes than the mainstream, knowing they are being observed and fearing of coming across as different.
Next thing you know, you have a society where everyone behaves uniformly, where differences are not tolerated anymore and where democracy has disappered.
You don’t need to know German to understand this clip:
Granted, Facebook is not to be compared to a “surveillance state”, but the tactics it uses to get its users slowly but surely “used” to its practices, certainly sound very similar to the tactics used by a surveillance state to achieve its objective.
I wonder what machiavellistic justification Facebook will come up with to explain this latest move. In this case, it cannot use the old ruse that it wants to provide its users a “better user experience”. For someone wishing to use a social networking site to do social networking, the move of restricting the amount of people with whom one can network socially can not seriously be thought of as providing a “better user experience.”
Have you noticed that you are only seeing updates in your newsfeed from the same people lately? Have you also noticed that when you post things like status messages, photos and links, the same circle of people are commenting and everyone else seems to be ignoring you?
Don’t worry, everyone still loves you and nobody has intentionally blocked you. The problem is that a large chunk of your friend/fan list can’t see anything you post because the “New Facebook” has a newsfeed setting that, by default, is automatically set to ONLY SHOW POSTS FROM PEOPLE WHO YOU’VE RECENTLY INTERACTED WITH OR INTERACTED WITH THE MOST (which would be limited to the couple of weeks just before people started switching to the new profile).
So in other words, for both business and personal pages, unless your friends/fans commented on one of your posts within those few weeks or vice versa – you are now invisible to them and they are invisible to you!
HERE’S THE FIX:
Scroll down to the bottom of the Newsfeed on your HOME page and click on “Edit Options”. In the popup, click on the dropdown menu next to ‘Show posts from:’and select “All Of Your Friends and Pages” and then click Save.
Note: This is the fix for personal pages but I am unsure of whether or not the business pages are set up the same way.
Simply posting an update about it won’t do any good because lots of your friends/fans already can’t see your posts by default. You’ll either have to send out a message to everyone on your list (which I’m not even sure business pages can do and is a rather tedious method) or post an event explaining the situation like this one and invite your entire fan base and/or friend list. You can also tweet about it hoping that most of your fellow facebookers are also on twitter.
PLEASE FEEL FREE TO SHARE THIS NOTE WITH AS MANY PEOPLE AS YOU CAN SO WE CAN TRY AND GET EVERYONE INFORMED AS SOON AS POSSIBLE. Anyone who isn’t seeing your posts right now will never see them until they have changed their settings as explained above.
Here is a screenshot I took of my Facebook Home page to illustrate Tracie’s excellent explanation:
As you can see, my default setting was set by Facebook to show posts from”Friends and pages you interact with most”. Of course, I changed it immediately to show posts from “All your friends and pages”. None of my Facebook friends were aware of this default setting, and most of them are professionals, very well informed in social media matters.
After changing the default setting, I learned that one of my friends’ daughters was Bat-mitzvahd, through a post that was hidden from me before I changed that setting, because this friend very rarely posts on Facebook. Another Facebook friend learned, only after changing her setting, that her cousin had a new baby.
This latest move by Facebook seriously worries me:
In my opinion, it smacks of censorship as practiced by the worst kind of despots. By introducing this kind of default setting and , on top of that, by not notifying users of this change, Facebook is basically deciding for its 600 million users what they can and cannot see on its platform.
What is the motivation behind this latest change? More profit for Facebook, no doubt, even though I fail to grasp the exact logic behind it.
I have understood by now, that as much as I want to believe, (or maybe Facebook wants me to believe) that I am the one using Facebook for my benefit, it is in reality Facebook that is using me for its benefit.
Facebook’s tactics of taking away our privacy and our choices, little by little, reminds me of the tactics used by the most dangerous tyrants in human history.
This excellent German video about the dangers of a sureveillance state, illustrates those tactics, as applied by governments.
It explains the traditional metaphor of the frog: when frogs are put in a tub of hot water, they instinctively jump out, because it hurts too much (except on Glenn Beck’s show, where they die instantly). Frogs that are put in a tub of cold water stay, even after the temperature slowly increases until they cook alive. So it is with people. When surveillance is increased slowly, people don’t revolt. They just adapt, and refrain from showing and exptressing differing attitudes than the mainstream, knowing they are being observed and fearing of coming across as different.
Next thing you know, you have a society where everyone behaves uniformly, where differences are not tolerated anymore and where democracy has disappered.
You don’t need to know German to understand this clip:
Granted, Facebook is not to be compared to a “surveillance state”, but the tactics it uses to get its users slowly but surely “used” to its practices, certainly sound very similar to the tactics used by a surveillance state to achieve its objective.
I wonder what machiavellistic justification Facebook will come up with to explain this latest move. In this case, it cannot use the old ruse that it wants to provide its users a “better user experience”. For someone wishing to use a social networking site to do social networking, the move of restricting the amount of people with whom one can network socially can not seriously be thought of as providing a “better user experience.”
Privacy and Data Protection in the EU: The grass is not always greener on the other side of the pond
February 4th, 2011 by Monique Altheim
According to the annual report of the French Association of Data Protection Officers (AFCDP), published
on 28 January 2011, 82% of French enterprises do not abide by the
French Data Protection Act of 2004 (La Loi Informatique & Libertés).The AFCDP is a professional organisation that represents French privacy professionals. The AFCDP works to develop privacy best practices and to build relationships with the French National Data Protection Commission (CNIL).
Following French Data Protection Act, an individual may request that an entity that holds personal data about him, share that personal data with him. After a request is made, the entity has two months to provide full information to the person who made the request, free of charge. In certain circumstances, the individual may then request that the personal information be deleted or that it be brought up to date.
The AFCDP published a second “Access Right Index”. It is intended to help French entities, both private and governmental, prepare themselves to respond to these information requests and to help educate individuals about their rights. The Index provides some insight into the manner in which entities are currently complying with the law.
To complete the study, access to personal data requests were sent to a panel of more than 220 French entities. In the Index, the AFCDP indicates which sectors were the best and worst in terms of compliance, and also provides anonymous, real examples of wrongdoing and guidance as to best practices.
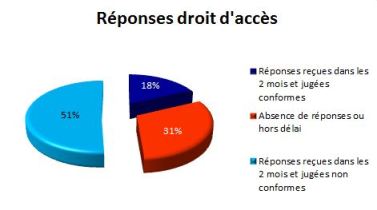
Here are some results of that study:
Only 18% of the polled organisations responded in a legally satisfactory manner to information access requests.
31% did not respond within the legal time frame. ( two months).
51% responded within the legal time frame, but not in a legally satisfactory manner: Some responded as follows: “The requested information cannot be communicated because it is the property of the company.”
The French Data Protection Act of 2004 provided, among others, the creation of a Data Protection Correspondent role in public and private organizations, the Correspondants Informatique & Libertés (CIL) . The appointment of CILs is not obligatory, but it facilitates the procedures for processing of personal data for the companies that do appoint a CIL.
Even among the companies that have opted to appoint a CIL, the compliance numbers are far from satisfactory: only 40% of the polled companies with CILs have responded to access requests in a law abiding manner. For example, some of these companies sent a gift to the requesting party, instead of the data. Others sent an announcement that the data were deleted, followed by an announcement of miraculous recovery plus a demand for a significant “recovery fee” to access the information.
The CNIL is, like so many of its counter parts in other EU member states, currently under significant pressure to cut operating expenses.
If it does not enforce the Data Protection Act, what use is it?
This very useful survey by the AFCDP illustrates how the passing of data protection acts alone is totally useless, unless these laws actually get enforced.
And if legislation does not even guarantee significant compliance, what kind of compliance will “self-regulation” achieve?
Congress, take note!
No comments:
Post a Comment