Global Data Protection, ECPA and Privacy Policies at the Computers Freedom and Privacy Conference 2011
June 18th, 2011 by Monique Altheim
On June 15, Peter Hustinx, the European Data Protection Supervisor, held a press conference,
where he emphasized the importance of the reform of the legal framework
for data protection in the EU. One of the many reforms mentioned, was
the reinforcing of international instruments in data protection.At the International Data Conference in Budapest on June 16, the European Commission stated that its proposal for a revised EU legal framework for data protection will be finalized this summer and published in November., and that it would promote the global dimension of data protection.
On the other side of the pond, in the U.S., Senator Patrick Leahy,the chairman of the Senate Judiciary committee, introduced, only a month ago, the Electronic Communications Privacy Act Amendment Act of 2011, that would bring the data protections against government access guaranteed by ECPA of 1986 up to date in a changed world of advanced technology and global economy.
Meanwhile, the subject of data mining, while practiced for a while by both private sector and governments, has received a renewed interest, due to ever increasing technological advances such as geotracking, mobile devices and biometrics.
How do the EU Data Protection framework overhaul, the ECPA revision proposal and data mining practices affect the average US consumer?
Find out by listening to this panel, presented at the 21st Annual Computers Freedom and Privacy Conference – The Future is Now, held at the Georgetown Law Center on June 14-16, 2011.
The panel was moderated by J.Bradley Jansen, Director at Center for Financial Privacy and Human Rights, and the panelists were: Monique Altheim, Esq., CIPP, at EDiscoveryMap, Ross Schulman, Public Policy and Regulatory Counsel, Computer & Communications Industry Association, and Steve Meyer, Director at Chain of Evidence.
Twitter Weekly Updates for EUdiscovery
June 17th, 2011 by Monique Altheim
- #CFPConf @tamir_i : urges the US to establish global privacy guidelines to catch up w. rest of the world. #
- #CFPConf @cedric_laurant: lack of integrity among EU Commission/ OBAs re finding privacy solutions; calls for accountability & real choice #
- #CFPConf @cedric_laurant : study showed that only 0.06% saw and clicked on adchoice icon #privacy #
- #CFPConf Last panel: Are we at a privacy tipping point- Jeff Chester http://t.co/2Hqi08h #
- Winners of #CFPConf 2011 research poster session moderated by Jeremy Epstein #privacy #facebook http://t.co/R4VWML7 #
- #CFPConf Schneier: currently science cannot assure cybersecurity; concentrate instead on resilience of systems #
- Bruce Schneier talking abt Cyberwar at #CFPconf http://instagr.am/p/F0-x_/ #
- #CFPConf David Bond going crazy trying to save his privacy by escaping into the wilderness #erasingdavid http://t.co/HFYKQt7 #
- #CFPConf Erasing David/David Bond; about surveillance society in UK #cctv #biometrics #privacy #
- #CFPConf Finally watching Erasing David by David Bond # privacy #
- RT @christinazaba: I've just posted Plenary: Cybersecurity, Freedom and Privacy on the #cfpconf blog http://tinyurl.com/62mnttf #
- RT @christinazaba: Keynote Address: Alessandro Acquisti http://tinyurl.com/5tjf7d6 posted now on the #cfpconf blog! #
- RT @christinazaba: I've just posted Plenary: Cybersecurity, Freedom and Privacy http://cfp.acm.org/wordpress/2… (cont) http://deck.ly/~8ausc #
- RT @CFP11: #CFPconf #CFPconfb Jay Stanley showing film of police helictopters fiilming couple's lovemaking wth infrared cameras #
- #CFPconf #CFPconfb Automating Policing Functions Panel pic http://instagr.am/p/F0hA1/ #
- #CFPConf Cybersecurity, Freedom and Privacy Panel moderated by Marc Rotenberg Pic http://t.co/Z9Vtto7 #
- RT @christinazaba: #cfpconf report >> A Clash of Civilizations: The EU and US Negotiate the Future of #Privacy http://t.co/1QWZTLh #
- RT @CFP11: #CFPconf day 3: watch it live on webcast, starting 9am ET http://tinyurl.com/3ue4xrg #computers #internet #infosec #
- #printempsarabe #Tunisie RT @CFP11: Watch @meryemmarzouki 's #CFPconf panel on the #arabspring on live webcas… (cont) http://deck.ly/~fa3ql #
- #CFPconf RT @CenDemTech: Great job @PrivacyWonk: Ten pieces of #privacy focused legislation from the 112th Congress http://bit.ly/joUKlO #
- RT @PrivacyWonk: Franken and Blumenthal drop mobile #privacy bill! http://wapo.st/kpRsfG #cfpconf #privchat #
- RT @AdamThierer: related to #CFPconf panel on intermediary liability, here's my map of new threats to Section 230: http://bit.ly/lTGukC #
- RT @PrivacyWonk: Franken and Blumenthal drop mobile #privacy bill! http://wapo.st/kpRsfG #cfpconf #privchat #
- RT @CFP11: #CFPconf pictures on Flickr http://tinyurl.com/5rusrub #privacy #infosec #internet #
- Lunch at #CFPConf with @DanielSolove , Annie Anton & Peter Swire http://t.co/lFNFYLw #
- If you missed the panel w. @moniquealtheim & @rossshulman ( Privacy Policies), hre's the podcast http://bit.ly/ifJZS6 #CFPconf #privacy #
- RT @CFP11: #CFPconf panel "Privacy Policies" Pic http://bit.ly/ma6FoS #dataprotection #
- #CFPconf webcast, Day 2 http://bit.ly/mcyQRO #privacy #internet #
- #CFPConf Multi Media Team Picture @CFP11 conference.#privacy yfrog.com/h0mlnfvj #
- CFP cartoon, day 1 RT @ReplyAllComic: Information Conferences. Heh heh heh. http://twitpic.com/5bpacb #CFPConf #
- RT @CFP11: awesome cartoon! RT @ReplyAllComic: Information Conferences and Why We Love Them: Reason #72 http://twitpic.com/5bnum4 #CFPConf #
- RT @ReplyAllComic: Information Conferences. Heh heh heh. http://t.co/s10geWg #CFPConf #
- #CFPConf Multi Media Team @CFP11 conference. Blogs, pics & videos to follow #privacy http://t.co/rvTaR0A #
- #CFPconf RT @CFP11: @CenDemTech hosts Dubliner Mass Avenue for those @CFP11 http://bit.ly/kK8SdY #
- I'll be speaking on the panel "Privacy Policies" in room B at 2pm #CFPconf #privacy #
- Do Not Track panel #CFPconf http://instagr.am/p/FuG8V/ #
- Packed audience at #CFPConf Do Not Track Panel #privacy http://t.co/9V7KRKy #
- Live webcast of lively Do Not Track Panel! http://bit.ly/mcyQRO #CFPconf #privacy #
- Schmiedel: it would be nice if US gave reciprocity to EU re #dataprotection #CFPconf #privacy #
- #CFPconf @JanAlbrecht : common data protection rules EU/US necessary to prevent recurrence of Europe's dark past. #totalitarianism #privacy #
- RT @CFP11: Live webcast of Barry Steinhardt's EU/US negotiations panel http://bit.ly/mcyQRO #CFPconf #privacy #surveillance #
- #CFPconf Barry Steinhardt panel EU/US negotiations http://instagr.am/p/FtrFq/ #privacy #
- #CFPconf Barry Steinhardt panel EU/US negotiations http://instagr.am/p/FtrFq/ #
- RT @CFP11: #CFPconf in DC starting today! Multimedia coverage here http://bit.ly/kIfqTN #privacy #dataprotection #internet #
- RT @CFP11: First day of #CFPconf Follow on webcast http://bit.ly/mcyQRO #privacy #dataprotection #
- RT @JulesPolonetsky: tag for CFP tomorrow! #CFPconf cu there! #privacy #
- +1 RT @PrivacyCamp: +1 RT @privacywonk: Looking forward to #CFPconf tomorrow. Anyone from #privchat attending? ^sd #
- RT @CFP11: Breakfast & Registration for #CFPconf tomorrow 7:30- 8:30 http://bit.ly/k6Uytj #privacy #internet #infosec #
- #CFPconf Senator Leahy Introduces the Personal Data Privacy and Security Act of 2011http://bit.ly/lNl9ie c and http://bit.ly/ezUk0Q #
- thnx! “@Privacymatters: #FF @bsookman @AppPrivacy @PrivaSense @guppiefish @privacyint @cedric_laurant @sunil_abraham @EUdiscovery @ksunea” #
- I'll be speaking on a CLE cert. panel @ #CFPconf on privacy policies in a global world with @RossSchulman http://bit.ly/iHfUyw #privacy #
Twitter Weekly Updates for EUdiscovery
June 10th, 2011 by Monique Altheim
- Commerce Department Calls for Improved Cybersecurity Through Voluntary Self-Regulatory Standards http://bit.ly/lOOvYo #
- RT @EgressSwitch: #ICO fines Surrey Council £120k for breaches of #DataProtection Act in 3 cases of misdirected e-mails. http://t.co/Wo75BOO #
- RT @iBridgeLLC: Not again!: Citi customer data exposed in online breach http://bit.ly/mRkPh0 #data #dataprotection #databreach #
- RT @BizMediaLaw: Netflix, Foursquare, and LinkedIn Android apps expose your password http://t.co/0fPdDub #privacy #
- RT @subatomicdoc: Facebook rolls out facial recognition tool in most countries http://t.co/knrkHdw via @tnwfacebook #privacy #
- #privchat Thanks @CenDemTech Don't forget:3 days left for #CFPconf registration! http://bit.ly/h9x1wq #
- #privchat A4: see my article on Yahoo Adchoice icons http://ediscoverymap.com/2011/03/948/ #
- I have, you need a microscope RT @econwriter5: Huh. Haven't seen these icons. #privchat #
- #privchat A4; the ones i saw were miniscule, and i had to click numerous times to get to page take action #
- #privchat A4: only if they are user friendly #
- #privchat RT @PogoWasRight: A3: My other big #privacy concern is US govt access to data if #ECPA and law not updated. #privchat #n #
- #privchat I believe it was a privacy issue. Nothing new abt the behavior, except the exposure RT @jim_adler… (cont) http://deck.ly/~zUjp6 #
- I believe it was a privacy issue. Nothing new abt the behavior, except the exposure RT @jim_adler: A2 ….@jwe… (cont) http://deck.ly/~VVBDr #
- #privchat A2 I read he mistakenly tweeted instead of DMing . Happens often.Has to learn how to use sms properly. #
- hope i wnt need a microscope 2 C them RT @PrivacyCamp: Behavioral Icon Appears in Political Ads http://ow.ly/5c2I1 #privacy #privchat #pdf11 #
- RT @jeffrichardson: My thoughts on why lawyers will love the new iOS 5 for iPhone and iPad, due this Fall: http://bit.ly/lMF4Ar #
- What is Apple's huge data warehouse for? http://bit.ly/jqRPAO #privacy #dataprotection #infosec #
- Professor shares top 10 tips for protecting online personal info http://bit.ly/l8ehUz #privacy #
- Topic: Rep.Weiner and Soc.Media #Privacy RT @PrivacyCamp: Today at 12 N ET #PrivChat on #Privacy (pls rt) Topics? Tweet us using #PrivChat #
- Data Encryption On The Rise http://bit.ly/jKT319 #security #infosec #
- RT @modmyi: iTunes in the cloud. #
- RT @RachelLive: I'll be there RT @PrivacyCamp: #PDF11 DC folks. must see Event > Computers, Freedom and #pri
Twitter Weekly Updates for EUdiscovery
June 3rd, 2011 by Monique Altheim
- Thnx!! RT @ghostnev3d: These People Are Great: http://t.co/Ur8WjpW @Rofrankle @EUdiscovery @Blackout1256 @Allenstweets #
- RT @PrivacyCamp: Thoughts? > #Privacy Policies, What Good Are They Anyway? | Application Privacy http://ow.ly/58PNh #
- What a pity! watch out for #CFPconf blogs, tweets & videos covering the conference! RT @gohsuket: @EUdiscover… Read more #
- What a pity! watch out for #CFPcon blogs, tweets & videos covering the conference! RT @gohsuket: @EUdiscover… (cont) http://deck.ly/~nhNtS #
- Costa Rica Privacy Legislation Moves Forward http://bit.ly/ig5OMw #
- You don't know what you don't know #filterbubble #internet #freespeech #
- EU Slams Google, Microsoft and Yahoo Over #DataRetention http://bit.ly/mQUt41 #dataprotection #privacy #
- Korea Announces Regulations to Personal Information Protection Acthttp://bit.ly/lYkPPm #privacy #
- RT @gohsuket: did it in 90's. miss it RT @CFP11 Who's willing 2 shoot sum vid clips 4 the #CFPconf ? will ge… (cont) http://deck.ly/~d2hT3 #
- RT @CFP11: Who's willing to shoot some video clips for the #CFPconf ? will get free registration to this 3-day DC conf. http://bit.ly/iWf5tY #
- Lack of Data Security and Protection in E-Discovery http://bit.ly/mRpmeG #ediscovery #
- Preliminary Thoughts about the HIPAA Accounting of Disclosures NPRM http://bit.ly/ivIy0A via @privacyprofessor #
- RT @CFP11: #CFPconf RT @ashk4n: Sony and Epsilon Agree to Testify Before Congress on June 2 regarding recen… (cont) http://deck.ly/~lUleF #
- RT @ashk4n: RT @random_walker Windows Skype users get 3rd party app installed by default ovr the wknd http://b… (cont) http://deck.ly/~nGgnE #
- RT @CFP11: Remember to register for #CFPconf Early registration ends today! http://bit.ly/ezUk0Q #socialmedia #cybersecurity #cloud #
- EDPS criticises #DataRetention Directive http://bit.ly/jTyPkG -hot topic @ #CFPconf panel with @JanAlbrecht… (cont) http://deck.ly/~cA6Os #
- RT @CFP11: Remember to register for #CFPconf Early registration ends today! http://bit.ly/ezUk0Q #ehealth #HIPAA #databreach #internet #
- HHS Issues Notice of Proposed Rulemaking for Accounting of Disclosures of Protected Health Information http://bit.ly/l8WiZm #HIPAA #
- thnx! RT @Tips4Tech: Shout-out waves @EUdiscovery @drogersuk @wireheadlance @sarakamal @hensel @berenicering @dqfozzie @LindaCriddle #
- RT @clarinette01: The #privchat Daily is out! http://bit.ly/brSO8h ▸ Top stories today via @cendemtech @cfp11 @prc_amber @jdp23 #privacy #
- German DPAs Publish Comprehensive FAQs on Statutory Data Breach Notification Requirement http://bit.ly/ju2JEa #databreach #
- interesting read! RT @CFP11: The Fourth Amendment in a Brave New World http://bit.ly/mF1cgH #CFPconf #privacy #SCOTUS #
- Progress made on digital agenda (EU) http://bit.ly/ivYc53 #internet #
- New Indian Privacy Rules 2 impact CIOs http://bit.ly/j5NIQj #dataprotection #
- RT @Tips4Tech: The Tips4Tech Daily is out! http://bit.ly/l28ATR ▸ Top stories today via @emilysteel @eudiscovery #
- One size fits all' EU data law would undermine rights, says Clarke (UK) http://bit.ly/jzWrCd #dataprotection #privacy #
- Does California Twitter Umasking Order Suggest the Application of Foreign Privacy Law in the US? http://bit.ly/ks0yyJ #dataprotection #
- Thnx! RT @PrivacyProf: gr8 Nfo! #FF @PogoWasRight @tips4tech @anthonymfreed @FortaliceLLC @intel_chris @EUdisc… (cont) http://deck.ly/~XD8bn #
- Check this video out — The Car http://t.co/kAsLDOj -my daughter made it for her production class #
- thnx!“@AppPrivacy: #FF @privacymatters @tapolicy @cfp11 @lossofprivacy @econwriter5 @racheloconnell@eudiscovery @paulhyland (via @ffhelper) #
- Thnx! RT @Steve_Widen: #FF @hensel @indreamer @sidneyeve @brianslatts @linkedmedia @tips4tech @berenicering @s… (cont) http://deck.ly/~lWs7h #
- Thnx & great w/e !RT @Tips4Tech: Shout-out waves @SueScheff @EUdiscovery @igirlpower @drogersuk @HighlightTec… (cont) http://deck.ly/~bglkK #
- RT @CFP11: Have a wonderful Memorial Day WE! Remember to register for #CFPconf Early registration ends 6/1 http://bit.ly/ezUk0Q #
- Can Covered Entities Take Advantage of the Cloud and Still Comply With HIPAA? http://bit.ly/ikscha #privacy #
- Directory of Major Brands & Retailers Selling on Facebook http://t.co/TqY47If #FCommerce #socialcommerce #
- Likester Takes Pop Culture’s Pulse — With Facebook Data http://bit.ly/kMt3zU #
- U.S.-E.U. Anti-Terrorism Air Travel Data Deal Is Faulted http://nyti.ms/mBvLUK #PNR #privacy #security #
- RT @zephoria: Jeffrey Rosen & i'll host @EPICPrivacy Champion of Freedom Dinner / Fundraiser. Please join us: http://bit.ly/mCZhzp #
- Can We Just Admit That The Idea Of A 'Privacy Policy' Is A Failed Idea? http://bit.ly/jojqBG #
- The College Board and ACT sell student names and information 33 cents a name http://bloom.bg/kuf979 #Markey Barton #FERPA #privacy #
- HIPAA, HITECH Compliance Not Improving Health Care Data Security: Survey http://bit.ly/kkOA8D #privacy #dataprotection #
- Asperger's charity loses children's data in laptop theft (UK) http://bbc.in/jMk6E4 #privacy #dataprotection #
- Thnx! RT @igirlpower: @Tips4Tech #FF hugs 4 safety @SueScheff @Steve_Widen @anthonymfreed @ovejaregia @Digital… (cont) http://deck.ly/~VA6Zk #
- Thnx! RT @Privacymatters: #FF @clarinette02 @eudiscovery @appprivacy @ashk4n @bsookman @AdamThierer #
- Thnx! RT @10comm: #FF many gr8 twttr contacts last week, handpicked 4 difft reasons: @anjakovacs @EUdiscover… (cont) http://deck.ly/~Rm3nx #
- RT @CFP11: Looking for multi media volunteers to cover #CFPconf online http://bit.ly/iWf5tY (free registration) -please RT #
Twitter Weekly Updates for EUdiscovery
May 27th, 2011 by Monique Altheim
- “Too many cooks spoil the broth.” #informationgovernance #datagovernance http://bit.ly/lwKPF3 #
- How safe is it to walk around wth your (Google) wallet in your hand? Would you walk around wth your credit card in hand? #security #
- RT @HuffingtonPost: Will Google Wallet really make a difference? http://huff.to/isuOvV #
- EU air passenger data deal with US defended by Kenneth Clarke (UK) http://bit.ly/m3NqW2 #PNR #privacy #
- social engineering tool? RT @gwynnek: Clever people and brilliant statisticians can see patterns that tell alot. Jason Hong-#sotmn #
- the groping war“RT@Drudge_Report: TSA Threatens To Cancel All Flights Out Of Texas If ‘Groping Bill’ Passed… http://t.co/LJCBdng” #
- #eG8 Q from public: where is the discussion on EU values re #internet Ou est la discussion a propos des valeurs ? #internet #
- Will the topic of #privacy even come up @ the #eg8 platform discussion w. Zuckerberg ? #dataprotection #security #
- RT @CFP11: Zuckerberg: I never said that kids <13 shld be on FB// Je n’ai jamais declare que les enfants <13 doivent joindre FB #eg8 #
- Zuckerberg: next big thing is social experiences, like gaming #zynga //l’avenir: les experiences sociaux, p.e. le jeu #zynga #eg8 #
- Sarkozy’s Web initiative faces reality check http://reut.rs/iGMM9W #eg8 #eg8forum #
- Zuckerberg in a suit RT @francetvdirect: Les photos de la rencontre entre Nicolas Sarkozy et Mark Zuckerberg #eG8 http://bit.ly/mk8v5K #
- Microsoft fights record EU fine ($1.3 billion), accuses Brussels of witch hunt http://bit.ly/j9vPBq antitrust #
- we need privacy diplomacy! @Privacymatters: The CNIL deplores the absence of DPAs from #eg8forum
- As YouTube Turns 6 Years Old, Daily Views Shoot Up To 3 Billion (Yes, 3 Billion. Daily.) http://tcrn.ch/jUW4Gc by @robinwauters
- RT @iconews: Appreciate concerns surrounding revised eprivacy & cookie laws, advice for orgs athttp://bit.ly/l8rouf(preview) or via our helpline – 0303 123 1113
- RT @omertene: McKinsey Report on “Big Data”. #privacyhttp://bit.ly/j77sCO(preview)
- @AppPrivacy:.. > Group Looks to Help App Developers Create #Privacy -Friendly Policies – AllThingsD http://ow.ly/53I9x #SOTM
- RT @CFP11: #CFPconf needs volunteers; free registration for volunteers http://bit.ly/j3T0aW please RT
- RT @declanm: Feds want to store U.S.-Europe passenger data for 15 years. (!) http://guardian.co.uk/world/2011/may/25/us-to-store-passenger-data #cnet
- RT @privacyfocused: Privacy Lives: New York Times: G-8 Leaders to Call for Tighter Internet Regulation http://bit.ly/l9Fqzs
- RT @gohsuket: ! RT @bendrath: Leak: EU EU-USA: Draft Agreement on the use and transfer of Passenger Name Record data to the US DHS… http://deck.ly/~TvCaw
- RT @EUinnovation: tech: Gagging orders: Twitter prepared to hand over user data http://bit.ly/iXZlGy #telegraph
- RT @NeelieKroesEU: Interested in my remarks on what we need to do to protect & empower children to benefit from the digital world? http://bit.ly/mnqZKi
- RT @OxonDataProtect: Euro. Comm. – Vast majority of EU countries “ignore” new #privacy & #dataprotection law on #cookies and consent http://tinyurl.com/4ymrxww
- RT @outlawnews: New law on cookies, data breaches and ICO powers comes into force today http://bit.ly/lyiR6g
- RT @MaasJonathan: Twitter’s new EU boss suggests users who break privacy injunctions by posting on site could face UK courts: http://tinyurl.com/3tsemz4
- RT @jfehrman: Morgan Stanley Brokers Will Use #Twitter & #LinkedIn To Market Themselves http://on.mash.to/jg3MAi #socialmedia
- RT @LexInformatica: New law on cookies, data breaches and ICO powers comes into force today: http://bit.ly/mP8eb5
- RT @ThePrivacyTrap: Most EU countries quietly ignoring new privacy laws http://trap.it/Z2esv8 #privacy
- the groping war“RT@Drudge_Report: TSA Threatens To Cancel All Flights Out Of Texas If ‘Groping Bill’ Passed… http://t.co/LJCBdng”
- RT @jonahlehrer: How vivid ads implant false memories http://t.co/gWkKLZdRT
- RT @ForbesTech: EXCLUSIVE: Facebook To Launch Music Service With Spotify http://j.mp/jiSbGh [post by @parmy] @techmeme
- RT @ThePrivacyTrap: Banks breach data rules with ‘alarming regularity’, says consumer group http://trap.it/xsHEBY #privacy
- @10comm: Civil Society Statement on eG8 and G8 – http://urlite.de/eG8 | in English, French, Spanish, link to German #eg8
- more
Twitter Weekly Updates for EUdiscovery
May 20th, 2011 by Monique Altheim
- European Commission Vows to Simplify #DataProtection http://bit.ly/ir43v6 #privacy #
- Google Brings TRUSTe Certification To Apps Marketplace — http://t.co/3Tqcx3W #mobilepriv #privacy #
- EU Demands Explicit Geo-Location Permissions | http://t.co/96NHmjw #mobilepriv #privacy #
- Apple and Android phones face strict laws in Europe: report (Reuters) http://bit.ly/joN1HY #mobilepriv is not only a US issue #
- RT @CFP11: CFP 2011 Conference To Address The Future Of Technology And Human Rights (via EDRI) http://bit.ly/kdFVvs #CFPconf #
- Art. 29 WP Opinion 13/2011 on Geolocation services on smart mobile devices http://bit.ly/m2FixW #privacy #mobilepriv #
- Art. 29 WP Opinion 13/2011 on Geolocation services on smart mobile devices http://bit.ly/m2FixW #privacy #dataprotection #
- CFP 2011 Conference To Address The Future Of Technology And Human Rights http://bit.ly/kdFVvs via EDRI #CFPconf #
- Why you can't really anonymize your data http://oreil.ly/jU26jW #privacy #dataprotection #ehealth #
- Final PHI Protection Rule Won't Mandate Encryption http://bit.ly/iDqM1D > not even for all the stolen laptops? #HIPAA #privacy #
- New Research Reveals Financial Data At Serious Risk During Application Development http://bit.ly/m5JbPF #privacy #security #
- FCC steps into privacy debate over location-based data, announcing forum http://t.co/QROYJrU via @latimestech #
- #CFPconf RT @AppPrivacy: BBC News – Google chairman Schmidt promises #privacy controls http://ow.ly/4XA0v #
- RT @CFP11: Early bird , great discounts, registration for #CFPconf ends in 2 days! http://bit.ly/h9x1wq #privacy #infosec #internet #freedom #
- Data Retention In EU Council Meeting http://bit.ly/jmfw6e #dataprotection #privacy #
- “@SarahCentrella: Court ordered that Facebook re-produce ESI in native format. http://t.co/wwipmyi” #ediscovery #
- Groups worry DHS pushing EU to weaken privacy protections http://bit.ly/mPp9GD #dataprotection #PNR #
- Should Facebook Data Be Private By Default? (CA bill SB 242) http://bit.ly/kT0xmL #privacy #
- EFF Applauds New Electronic #Privacy Bill That Tells the Government: Come Back With a Warrant! http://bit.ly/kyF1of #ECPA #
- Thansk for RTs @SophieToupie @nicoschunter @LossofPrivacy @DianeBarry @rigow @gohsuket @TechIsMidlName #
- Thanks for Rts @bitsofprivacy @ProfJonathan @PrivacyInfo @Privacymatters @fak3r @MirskyLegal @privacyfocuse… (cont) http://deck.ly/~07k4o #
- "Street View, Privacy, & the Security of Wireless Networks"5/18 U.S. Capitol Visitor Center http://bit.ly/imO5DX #wifiprivacy #privacy #
- Comprehensive Personal #DataProtection Law Enacted in Korea http://bit.ly/lUsedm #privacy #
- Fed. Privacy Legislation Not Expected Anytime Soon: Experts http://bit.ly/iR6XmL – or "It is difficult to ge… (cont) http://deck.ly/~46fDQ #
- RT @RyanRadia: Leahy's #ECPA Reform Bill text is here (PDF): http://1.usa.gov/lU6wTK #privchat #
- FTC's Vladeck: More Privacy Actions On The Way http://bit.ly/liKSok #
- Hustinx (EDPS) Says Location Data Is Personal Data http://bit.ly/k0Zq6o #privacy #dataprotection #mobilepriv #
- RT @mostrolenk: #Privacy #EU 11 Privacy & Civil Liberties Groups Urge U.S. 2 Uphold Privacy Values in E.U. Negotiations http://bit.ly/kos4wh #
- Top US officials defend passenger name exchange system (PNR) in Brussels http://bit.ly/jhPjRw #privacy #dataprotection #
- RT@CFP11 Early bird registration for #CFPconf ends in 3 days! http://bit.ly/h9x1wq #privacy #infosec #internet #
- French DPA (CNIL) Increases Compliance Inspections of U.S. Companies http://bit.ly/jeLEez #privacy #dataprotection #ediscovery #
- RT @PrivacyCamp: RT @senatorleahy: Intro bill to update electronic #privacy laws; proud to write ECPA 25 yrs… (cont) http://deck.ly/~ebahf #
- Then SB242 makes more sense RT @JustinBrookman: @EUdiscovery Under SB 242, you're right. Under Barton-Markey, I could. #privchat #
- Thanks all for great #privchat Don't wait! RT @CFP11: Early bird registration for #CFPconf ends in 3 days! http://bit.ly/h9x1wq #privacy #
- #privchat most people also don't opt-out of anything, & the industry counts on it @omertene @privacyfocused "People don't opt into anything" #
- #privchat I believe HE could, not you RT @JustinBrookman: Eraser buttons mean I could single-handedly destro… (cont) http://deck.ly/~TxteD #
- I believe HE could, not you RT @JustinBrookman: Eraser buttons mean I could single-handedly destroy Justin Bie… (cont) http://deck.ly/~6eeok #
- #privchat A4: what's the downside to requiring that all FB privacy settings set to maximum privacy by default? should be Federal Law! #
- #privchat A3: not enough focus on harmful economic consequences of datamining to consumers (jobs, health insurance, reputation) #
- RT@privacypug A3: Focus on DNT over comprehensive privacy regulation. #PrivChat #
- agreed, golden middle is best RT @spinzo: .@EUdiscovery @PRC_Amber @jim_adler But the answer isn't over-regulation. #PrivChat #
- #PrivChat anyone studied history of self-regulation? RT @PRC_Amber: @spinzo @jim_adler I think you are underes… (cont) http://deck.ly/~RAIxH #
- #privchat A2 : reliance on notice & consent outdated (who reads policies?), no private right of action, enforement by FTC problematic #
- #privchat A2: I like increase protection to 18, reliance on FIPPs and Eraser Buttons #
- #privchat EU is trying with PNR & SWIFT negotiations @BeatTheChip: I think the EU should protect their citizen… (cont) http://deck.ly/~D1X4F #
- EU is trying with PNR & SWIFT negotiations @BeatTheChip: I think the EU should protect their citizens from U… (cont) http://deck.ly/~kS5jU #
- Hi, Monique Altheim here #privchat #
- California Bill Targets Social Networking Privacy http://bit.ly/kzIk1X #socialmedia #dataprotection #
- Reading Chris Soghoian's FTC complaint v. Dropbox http://snipr.com/27wro4 so Dropbox changes policy & everything's OK? #privacy #security #
- Panel to Propose Tighter #DataProtection in Europe – http://nyti.ms/kC9jqo #privacy #mobiliepriv #
- Google Turns On Charm to Win Over Europeans – http://nyti.ms/mIVcKs #
- Who is dropping Dropbox over terms-of-service changes? http://bit.ly/mQkVXe #privacy #
- Personal Data: Most Top Apps Lack Privacy Policies http://bit.ly/mTRVd3 #dataprotection #
- RT @CFP11: The #Privacy Debate Should be a Conversation http://bit.ly/mfIkhg – Join the biggest one of them al… (cont) http://deck.ly/~wBkWW #
- KPN (NL) denies violating privacy rules by using DPI http://bit.ly/lN4TDq #dataprotection #
- Offshoring: Preparing for India's proposed privacy rules http://bit.ly/lrzVJL #
- German Federal Office for Information Security Issues Final Framework Paper on Information Security for Cloud Computing http://bit.ly/jTYmHr #
- thnx! “@TAPolicy: #FF @eudiscovery @ceciliakang @PrivacyCamp @appprivacy @ashk4n @JustinBrookman @CenDemTech @Bsegalis @techpolicy” #
- Offshoring: Preparing for India's Proposed Privacy Rules http://bit.ly/mp20Si #dataprotection #
- RT @kocobob: Find out how much your personal info is worth to data broker Rapleaf http://blogs.forbes.com/kash… (cont) http://deck.ly/~kYdAs #
- #dataprotection RT @_pidder_: EU to get tough on geolocation data #privacy http://is.gd/cHTcJz #
- RT @CFP11: Special hotel rate offer for CFP conference ends in 2 days! http://bit.ly/h9x1wq #privacy #infosec #internet #freedom #CFPconf #
- White House Releases Cybersecurity Legislative Proposal http://bit.ly/l3FwSM #
- Thanks for recent RTs @TAPolicy @obinine @GammaCounter @rigow @IntegroBurt @PrivacyInfo @ConsultScarab #
- Thanks for recent RTs @nicoschunter @jonathanchanUK @Privacymatters @JamesDShookEsq @rigow #
- Thanks for recent RTs @Tips4Tech @IntegreonEDD @DianeBarry @PSS_Systems @HowardMSklar @PrivacyCamp @fjcarbayo @dataprivacyrisk @canoewolf #
- Thanks for recent RTs @PetePepiton @fak3r @mvedelman @Alexandriallc @benkerschberg @gohsuket @cdlxls @bradykri… (cont) http://deck.ly/~FEz8E #
- Ford teams with Google for cars that can read your mind | TG Daily http://t.co/jSJxsZF #
- Government Developing Data Mining Tools To Fight Terrorism — InformationWeek http://www.informationweek.com/n… (cont) http://deck.ly/~18Zyn #
- Smart Phones, Trojan Horses & #DataProtection my latest blog post http://bit.ly/jlKWLz #privacy #mobilepriv #Whoopsyoualreadysaidthat #
- KPN (NL) Admits To Using Deep Packet Inspection http://on.wsj.com/iXzIYN #privacy #
- #Databreach suits grow, but damages hard to prove http://bit.ly/lsTXnt privacy #security #Sony #
- Apple Sued Over #Privacy Concerns, Again http://bit.ly/iSDkFk #
- Online Privacy: Can the U.S. Get Its Act Together? http://snipr.com/27uhpb #mobilepriv #dataprotection #
- Smart Phones, Trojan Horses & #DataProtection my latest blog post http://bit.ly/jlKWLz #privacy #mobilepriv #
- Twitter Weekly Updates for EUdiscovery http://t.co/nJAuul1#privacy#ediscovery #socialmedia #
Twitter Weekly Updates for EUdiscovery
May 13th, 2011 by Monique Altheim
- Thnx!RT @Privacymatters: #FF @AppPrivacy @EUdiscovery @sunil_abraham @PrivacyPrivee @ashk4n @bsookman @embedprivacy @ksunea @kashhill #
- Thnx!RT @gsmaprivacy: #FF @AppPrivacy @EUdiscovery @sunil_abraham @PrivacyPrivee @ashk4n @bsookman @embedprivacy #
- Does EU #DataProtection Law apply to Apple/Google/App developers ? This old story new again http://bit.ly/gOZ2ps #mobilepriv #privacy #
- Obama’s Cybersecurity Plan Urges More Disclosure of Breaches to Consumers – Bloomberg http://t.co/ldVhiyT via @BloombergNow #
- White House unveils cybersecurity proposal http://reut.rs/jCr4ol #
- CNIL (French DPA) announces increased inspections for compliance with French and EU data #privacy requirements http://bit.ly/kbJozT #
- EU Art.29 Working Party to Affirm Location Is "Personal Information".http://on.wsj.com/k8bEjG #dataprotection #privacy #mobilepriv #
- good morning! RT @CenDemTech: "Current law allows companies to share data however they wish as long as they do… (cont) http://deck.ly/~FapfA #
- UK ICO Releases Code on Data Sharing http://bit.ly/l6Ia4B #dataprotection #privacy #
- EU: 41% of IT professionals using mobile data without protection http://bit.ly/je02ns #privacy #security #
- Internet of Things Europe Conf. June 28-29, Brussels, http://bit.ly/fDubZK #IoT #
- #privacy #profiling #socialmedia RT @_pidder_: Entering The Minority Report Era: A video Series http://tnw.co/jurIEq #
- Domestic spying on Americans is an e-hoarding epidemic http://bit.ly/mKVWIr#dataprotection #privacy #
- RT @CFP11: HHS To Release Final Rule on #HIPAA #Privacy, #Security by End of Year http://bit.ly/ki3MvP #CFPconf #
- Why We Need "Do Not Track Kids" http://huff.to/mcsH4g #privacy #COPPA #dntrack #
- (UK) Police’s purchase of GeoTime tracking software will be misused, warn privacy groups http://bit.ly/k29iqO #dataprotection #surveillance #
- RT @CFP11: M.Rotenberg on Smartphone #Privacy Hearing http://bloom.bg/kaX5xS and on #cybersecurity #freedom … (cont) http://deck.ly/~rlnLO #
- RT @CFP11: Interview w. D. Peel: Protecting patient privacy rights in a wired world http://oreil.ly/jm69HU#ehealth #CFPconf #
- If your picture is newsworthy, think twice before posting it on Twitpic http://bit.ly/kvHl6j #Twitter #socialmedia #copyright #
- Call to extend EU rules on data breaches to all online companies http://bit.ly/l84vQa #dataprotection #databreach #privacy #
- Twitpic:Copyright belongs to user, but Twitpic reserves right to sell pics to third parties http://bit.ly/kXumLe #socialmedia #twitter #
- #ediscovery RT @nuix: eDiscovery Case Law: Written Litigation Hold Notice Not Required: http://ow.ly/4SfRS #
- RT @CFP11: AMC's CFP Conference registration in full swing. Early registration deadline 5/20! http://bit.ly/h9x1wq #infosec #CFPconf #
- Socha & Gelbmann's Apersee Emerges from Beta http://bit.ly/iwhBN9 #ediscovery #
- Toy Robots and Programmed Light Bulbs – Google Embraces the Internet of Things http://t.co/6uWX86T via @RWW #
- Best Buy suffers second data breach in a month http://bit.ly/muUGC2 #privacy #security #
- BBC News – Brighton activist to challenge police database – http://bbc.in/isI5pw #privacy #surveillance #
- ACS Law boss hit with #dataprotection fine (UK) http://bit.ly/mqnpxi #privacy #security #
- DOJ, FTC Suggest Mobile Privacy Changes http://bit.ly/kdEwd2 #dataprotection #ECPA #
- DOJ: Electronic Privacy Act (ECPA) Needs Better Balancehttp://bit.ly/j9eulp #dataprotection #
- New Director of DAA Plans for Global Rollout http://bit.ly/lE9cNR via @clickz #
- New Director of DAA Plans for Global Rollout http://t.co/wSth1Dl via @clickz #
- Google to appeal in Swiss Street View privacy battle http://bit.ly/jXnK94 #dataprotection #
- Apple, Pandora, Backflip sued over iPhone data privacy http://t.co/tbncu7H #dataprotection #
- RT @PrivaSense: #Facebook app bug overrides user #privacy settings, exposing millions of user credentials http://bit.ly/lSoCiC #security #
- iPhones and e-discovery: location data in a court of law http://bit.ly/k9ygIP #ediscovery #mobilepriv #
- WSJ.com – Google and Apple Defend Data- Privacy Controls http://on.wsj.com/jlrFRP #mobilepriv #
- #privacy RT @ashk4n: Plus the graphic I used demonstrating the accuracy of GPS vs Wi-Fi geo-location http://bit.ly/kQVxiv #mobilepriv #
- Live blog: Senate Judiciary Committee hearing on #mobilepriv http://usat.ly/kDuYlM #privacy #
- RT @CFP11: AMC's CFP Conf. registration in full swing. Early registration deadline 5/20! http://bit.ly/h9x1wq #privacy #infosec #CFPconf #
- and only in some states RT @Forsheit: Nope -MA 201 CMR 17, CA 1798.81.5, etc apply 2 all sectors RT @EUdiscove… (cont) http://deck.ly/~u6LTK #
- only in certain sectors RT @Forsheit: I don't agree-dozens of state & federal laws RT @EUdiscovery Brookman(CD… (cont) http://deck.ly/~4erse #
- J.Brookman(CDT): the default law in the US is that (personal) data can be shared with anyone #privacy #mobilepriv #
- Tribble(Apple): the fact that location tracking was operating even though users had opted out was due to a "bug"- ahem #privacy #mobilepriv #
- Senator Whitehouse compares mobile apps to Trojan Horses and FTC agrees #privacy #mobilepriv #
- Senator Leahy announces upcoming proposal to revise ECPA #privacy #mobilepriv #
- ICO publishes advice on how websites can comply with new 'cookie law'http://bit.ly/jjhXVM #dataprotection #EU #
- California Clarifies Smart Meter Privacy Rules http://t.co/7rUN3AQ via @greentechmedia #privacy #
- Policymakers can help increase confidence in the #cloud by protecting consumershttp://bit.ly/j31254 #
- Again? TomTom to sell aggregate GPS data (this time in Australia) http://t.co/hslaH55 #privacy #dataprotection #
- Privacy Groups Support Sen. Rockefeller's Do-not-track Bill http://t.co/vgWjBq6 #privacy #dataprotection #
- Implementation of EU data privacy rules (in U.K.) 'lacking clarity' – Telegraph http://t.co/ZPlRK8X via @Telegraph #privacy #dataprotection #
- Required Reading: What to Know Ahead of Today’s Apple/Google Hearing http://t.co/oZzYQ2H #privacy #
- Journalists do not have to pre-notify the subjects of stories, says European human rights court http://bit.ly/mrMXKx #ECHR #privacy #Mosley #
- Survey: 7.5M Facebook users below minimum age (13) http://cnet.co/imQvV5 #COPPA #privacy #
- RT @BillMcGev: Mobile #privacy hearing in Senate submte, chaired by @alfranken, webcast Tues. morning startin… (cont) http://deck.ly/~wsqzj #
- RT @privatewifi: There’s No Data Sheriff on the Wild Web: http://ow.ly/4PXB4 (via @nytimes) #privacy #security #
- learn how to zap RFID chips! RT @privacyfirst: Workshop RFID-chips vernietigen…http://bit.ly/iraHZ1 #privacy #
- another one! RT @emilymbadger: Do Not Track bill introduced in the Senate today: http://bit.ly/jsW3sN #privacy #
- ICO (UK): Changes to the rules on using cookies: browser settings NOT meaningful consent http://bit.ly/jLQtgR #dataprotection #privacy #
- Thnx RT @Tips4Tech: Shout-out #gratitude @RickBlaisdell @LindaCriddle @TechL0G @LARosen @lennyzeltser @Fortali… (cont) http://deck.ly/~LzDkk #
- EU: Striking a balance between “active and passive” information http://bit.ly/mQ219Q #freedomofinformation #privacy #
- Thnx! RT @LindaCriddle: #FF #Safety @marykayhoal @EUdiscovery @PrivacyProf @InfraGard808 @CyberSafety808 @808… (cont) http://deck.ly/~0EXfN #
- RT @IntegreonEDD: Ignorance is not bliss: knowing when to issue a litigation hold http://bit.ly/iFxqxh | vedderprice.com #ediscovery #
- Two More Online Privacy Bills to Hit Congress http://t.co/rqe13Fr via @clickz #
- RT @twechy: How to wipe personal data from your old phone – when you get a new one: http://su.pr/22sk6e #cellphones #privacy #
- Thnx!RT @SueScheff: @30secondmom @MedHealthNews @bingnote @pamslim @EUdiscovery @HeartlightGirls @AttorneyBlad… (cont) http://deck.ly/~fQvuB #
- Twitter Weekly Updates for EUdiscovery http://t.co/Bqds1Dj #ediscovery #privacy #socialmedia #
- I tweeted the title of the article @troy_norcross #
- Thnx! @Tips4Tech: #FF #tech @TechL0G @Steve_Widen @SueScheff @marykayhoal @LindaCriddle @EUdiscovery @PrivacyP… (cont) http://deck.ly/~ln3Pu #
- re: #shocktweets @troy_norcross you probably never heard how easy de-anonymization is. #
Smart Phones, Trojan Horses and Data Protection.
May 12th, 2011 by Monique Altheim
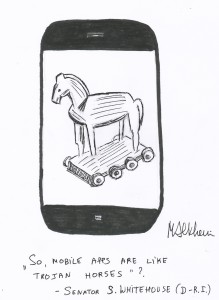
During the Senate Judiciary Committee hearing on mobile privacy, held on May 10, Senator Whitehouse asked Rich (FTC) and Weinstein (DOJ) if mobile apps were like “Trojan Horses” of consumer info.
What is a Trojan Horse?
The contemporary meaning of Trojan Horse, according to GSMA, is
“a specific form of malware [link to malware entry in ]. Like the Trojan Horse of Greek mythology, Trojan Horse programs trick a user into installing them on their phone or computer by masquerading as genuinely useful applications. Once installed however, the Trojan Horse will perform some unauthorised and malicious activity on the computer or phone. Trojan Horses are one reason why you should only install software on your phone or PC if you are confident that you can trust the source of this software. Trojan Horse programs differ from Viruses and Worms [link to appropriate entries in ] because Trojan Horse programs are unable to replicate themselves. Installing anti-virus software on your mobile phone can help to protect against this threat.”
From the context of the hearing, it would seem that Senator Whitehouse was referring to the original, albeit metaphorical meaning of “Trojan Horse”: the mostly free mobile apps are waiting in the app store to be downloaded by smartphone owners on their mobile phone; once the app is “inside” the phone, it “opens all the information gates” for the app developers, Apple, Google, advertisers, ad networks, the entire marketing ecosystem and a garden variety of hackers and stalkers.
Is this legal?
The consensus during the hearing seemed to be that it is. At least within the US.
Justin Brookman, director Consumer Privacy for the Center of Democracy and Technology, gave a comprehensive summary of relevant laws and an analysis of their application to today’s location- enabled mobile devices.
He concluded that “current law allows companies to share data however they wish so long as they don’t do something they previously promised not to, which would be a violation of the Federal Trade Commission Act.”
In other words: Except in certain sectors, like healthcare and finance, and except in a couple of states like Massachusetts and California, the personal data of smartphone (and general internet) users can legally be shared with anyone, without the data subject’s consent.
But the mobile world is global and flat, and does not distinguish between smartphone (or internet) users, depending on their geographical location: it tracks them all the same. Except that outside the U.S., many countries have strict data protection rules that make mobile (and general internet) tracking illegal, unless a list of conditions are met.
The European Data Protection Laws, and the national data protection laws of the EU member states, for example, require, among many others, notice and informed consent for tracking of all personal data, and explicit consent for tracking of sensitive data, relating to health, religious beliefs, political opinions, sexual orientation, race, and membership of organizations.
The current overhaul of the 16 year old EU Directive 95/46EC has exactly this global world in mind.
Viviane Reding, European Commissioner for Justice, Fundamental Rights and Citizenship, recently declared in the context of the EU Data Protection Law overhaul that “To enforce the EU law, national privacy watchdogs shall be endowed with powers to investigate and engage in legal proceedings against non-EU data controllers whose services target EU consumers,”… “Any company operating in the EU market or any online product that is targeted at EU consumers must comply with EU rules.”
Apple is already under investigation by data protection officials in Germany, France, Italy and Switzerland for possible breach of their national data protection laws.
Last year, Mexico joined the ranks of more than 50 countries that have enacted global data privacy laws by enacting a “Federal Law on the Protection of Personal Data Held by Private Parties” that for a large part copies the EU model.
More recently, India issued final regulations implementing parts of the Information Technology (Amendment) Act, 2008. These strict privacy rules also take after the EU data protection model and the penalties for non-compliance include imprisonment and fines.
Global companies like Apple and Google should take into account that an increasing number of their worldwide business partners’ and customers’ personal data are covered by national data protection laws, even though the personal data of their own poor fellow countrymen are not.
Twitter Weekly Updates for EUdiscovery
May 6th, 2011 by Monique Altheim
- Canadian Privacy Commissioners launch free assessment tool for businesses http://bit.ly/jXNsdF #dataprotection #
- India’s New Privacy Regulations (Morrison & Foerster Client Alert) http://bit.ly/jeLtAw #dataprotection #
- Should Patients Trust Their Doctors' EMR Systems? http://bit.ly/ln1PW6 #privacy #dataprotection #
- Your Medical Record is Likely for Sale, Doctors Warn http://prn.to/l8M1Cw #privacy #dataprotection #
- Netflix Fires Call Center Worker for Stealing Data http://t.co/QQejwZf #privacy #dataprotection #
- IT Outsourcing in China And Data Privacy Guidelines http://t.co/9AB2Fi4 #dataprotection #
- Canadian PlayStation users plan class action suit for hacking http://bit.ly/jQdiKk #privacy #security #
- #privacy -FTC settles charges agnst 2 Co. that compromised sensitive employee data http://1.usa.gov/k2OBBP -an… (cont) http://deck.ly/~zh5jN #
- RT @nytimesbits: Sony Explains PlayStation Attack to Congress http://nyti.ms/ieBxA8 #privacy #security #dataprotection #
- Witnesses trying very hard to defend geolocation data retention. Why? A Look at Threat of Data Theft | C-SPAN http://t.co/fWi4Gmr #privacy #
- A Look at Threat of Data Theft | C-SPAN http://t.co/fWi4Gmr #privacy #security #sony #
- California and Massachusetts Legislatures Push Data Breach and Security Bills http://t.co/stuZuOF #databreach #privacy #
- N.Kroes (EU) welcomes the public private partnership to forge the Internet of the Future (FI-PPP) http://bit.ly/k1cbtF #PPP #
- Google destroys Aussie Wi-Fi data http://bit.ly/lgQ4ZR #privacy #dataprotection #
- Smartphone Spying Reality Check http://t.co/KRv1PCW #privacy #dataprotection #
- Europe Seeks to Set Standard for Protecting User Data – http://nyti.ms/mt5tv6 #dataprotection #privacy #
- Authorities in Austria and Switzerland Rule on Google Street View http://bit.ly/kgOB0h #privacy #dataprotection #
- Sophia in 't Veld on US subpoenas and EU #dataprotection rules http://bit.ly/kIm40j #privacy #
- Judge dismisses Internet privacy case for lack of harm http://bit.ly/lJCIUV #
- Sony hit by second security breach by hackers http://wapo.st/l70kFx #privacy #dataprotection #security #
- South Korean Police Probe Google Over Location Data Collection http://huff.to/jIMp9o #privcacy #dataprotection #
- TomTom Will Tighten Data Sharing Rules http://on.wsj.com/jyXfoq #dataprotection #
- Obama killed Osama (watch my animation video!) http://youtu.be/-vTNop92R4c
 #
# - Obama killed Osama (cartoon) http://youtu.be/-vTNop92R4c #
- 6 Tips to Increase Your Facebook EdgeRank and Exposure http://bit.ly/jpnoBT #socialmedia #
- uncut version here
 http://bit.ly/j1QtQO RT@PrivacyCamp: OK . This is the MUST WATCH video of the wee… (cont) http://deck.ly/~eNBF0 #
http://bit.ly/j1QtQO RT@PrivacyCamp: OK . This is the MUST WATCH video of the wee… (cont) http://deck.ly/~eNBF0 # - Thnx! RT @CenDemTech: #FollowFriday #Privacy edition @PrivacyCamp @pr1vacy @EUdiscovery @AppPrivacy @PrivacyDi… (cont) http://deck.ly/~UhELm #
- It's official: Sony suffers massive data breach http://bit.ly/m7e7z6 #privacy #security #
- "Why It’s Important to Come Clean Now on Location Data" ( uhm, it's the right thing to do? no cigar) http://bit.ly/kJkwaf #privacy #
- #privacy #security RT @FamOnlineSafety: PlayStation Network: hackers claim to have 2.2m credit cards http://bit.ly/jhNmk1 #
- Twitter Weekly Updates for EUdiscovery http://t.co/X1wJk97 #privacy #ediscovery #socialmedia #
- ICO (UK) calls for tougher penalties for data trafficking http://bit.ly/lVgyHM #dataprotection #
- Over half of Indian firms store digital data abroad http://bit.ly/m4ZSJe #privacy @dataprotection #
- Is the EU ready to put its data in the clouds? – RTÉ News http://t.co/oxFVfjO via @rtenews #privacy #dataprotection #
- Apple, Sony Face Possible Action By EU Data Privacy Regulators http://bloom.bg/kUFtD1 #privacy #dataprotecetion #
Twitter Weekly Updates for EUdiscovery
April 29th, 2011 by Monique Altheim
- Holding Companies Accountable for Privacy Breaches (Epsylon, RSA, AT&T, Apple, Google, Microsoft, Sony…) http://nyti.ms/iCAJKw #
- Rep. Bono Mack (R-Calif.) to introduce #dataprotection bill http://bit.ly/jeZxGm #privacy #
- India, New privacy Bill: #DataProtection Authority, jail term for offencehttp://bit.ly/m9brr3 #privacy #security #
- Amazon’s Outage: Winners and Losers | SYS-CON MEDIA http://t.co/PkJ3s4j #
- PSN/social networks an easier target for hackers than banks http://bit.ly/iVWn7t #privacy #dataprotection #
- Sony may be hit with £500K fine over PSN data loss http://t.co/ca9nZfp #privacy #
- Apple’s storage of iPhone data raises Swiss privacy protection issues http://bit.ly/ldaJK5 #privacy #dataprotection #
- Study: 77% Don’t Want to Share Location on Smartphones by @rwwmike http://t.co/Cy6twna via @RWW #privacy #
- Why We Need An Open Wireless Movement https://www.eff.org/n/13340 #
- Survey: Mobile consumers most concerned about privacy – Mobile Marketing – BizReport http://t.co/MKndyYx #
- TomTom sorry for giving customer driving data to cops http://reg.cx/1NQD #privacy #
- Canada’s Privacy commissioner looking into Sony hack http://t.co/muMzXbS #privacy #
- Congressman wants FTC probe of iPhone tracking http://t.co/UyDYyW0 via @cnet #
- Jepsen Investigating Smart Phone Tracking, Sony Data Breach – Courant.com http://t.co/MH0dCyV #
- Marc Rotenberg Interview on Apple’s IPhone Data – Video – Bloomberg http://t.co/AigfolS via @BloombergNow #
- Africa likely to lead in mobile health http://bit.ly/hNMLBx #mhealth #privacy #
- I found the Apple iPhone bug! It’s called the kleptomaniax

- “The case is not about patients’ #privacy rights”- never heard of de-anonymization? Sorrell v. IMS Health http://nyti.ms/f6RMjA #SCOTUS #
- US Senator Blumenthal Demands Answers From Sony Over PlayStation Network Data Breach http://bit.ly/gO5Eib #privacy #
- Apple to Alter iPhone Data Collection http://nyti.ms/lPEMCW #privacy #dataprotection #
- Japan May Hold Individual Employees Liable for Violations of #DataProtection Law http://bit.ly/g9lEqY #privacy #
- Summary: ZDNet’s USA PATRIOT Act series ( on how the Patriot Act affects EU data) http://zd.net/lGy5ZR #privacy #dataprotection #
- RT @ComplexD: The Five Hottest Topics in #eDiscovery – http://tinyurl.com/3dsftg2 (Sharon Nelson, John Simek, Josh Gilliland) #
- RT @RTeDiscovery: Fantastic break down of Judge Peck’s Top issues for #ediscovery in 2011. ..http://ow.ly/4HXdI #
- (Short and smart) Will There Ever Be An “Internet Erase Button”? http://bit.ly/h6RsWA #privacy #
- RT @ActNowTraining: PlayStation hacker took user info – http://bbc.in/hfuKQ6 #dataprotection #privacy #
- RT @CenDemTech: Apple’s missteps on iPhone location file brings into clear focus the need for “#Privacy by Design” http://cdt.org/K4Y #
- CDT analysis of Commercial #Privacy Bill of Rights Act 2011 http://bit.ly/gh4B1V #
- French Data Protection Authority Unveils its Goals for 2011 Inspections http://bit.ly/fC06OE #dataprotection #privacy #
- + Happy Passover too RT @euHvR: Zalig Pasen, Joyeuses Pâques, Happy Easter, Frohe Ostern, Felice Pasqua, Feliz Pascua #
- RT @JulesPolonetsky: Passover Privacy Plea, let my data go
 Show Us the Data. (It’s Ours, After All.) http://bit.ly/idjd5Q?rqX #
Show Us the Data. (It’s Ours, After All.) http://bit.ly/idjd5Q?rqX # - Why you should turn off your smartphone’s geotagging feature when you post a picture online http://bit.ly/egWivs #privacy #
- Privacy in the Workplace: An Oxymoron? http://bit.ly/eOLumu #
- RT @nicfab: The New Tech Law Daily is out! http://bit.ly/eOxpxa ▸ Top stories today via @racheloconnell @melan… (cont) http://deck.ly/~nkSTM #
- Thnx! RT @Tips4Tech: #FF #legal #tech #privacy @EUdiscovery @Forsheit @DavidNavetta @bsegalis @InfoLawGroup @D… (cont) http://deck.ly/~rEaHa #
- How can US law enforcement agencies access location data stored by Google and Apple?http://bit.ly/huPCz8 #privacy #ECPA #
- Lost, Stolen Laptops Cost European Companies Billions in 2010 (study)http://bit.ly/ebqKio #privacy #security #
- Interactive murder mystery raises awareness about #dataprotection on German TV http://bit.ly/g1tTRJ (Wer rettet Dina Foxx?) #privacy #
- US senator questions Apple for using phone-tracking software http://bit.ly/hhsPDt #privacy #
- Update Your Skype for Android App to Protect Data http://bit.ly/fDN3I9 #privacy #security #
- Twitter Weekly Updates for EUdiscovery http://bit.ly/hge3lc #privacy #ediscovery #socialmedia #
- Maine debates privacy permissions for health data http://bit.ly/h7O6IW #privacy #ehealth #
Such a nice post, now i sharing tips and guide about..Data Protection While Traveling
ReplyDelete